
Splunk Enterprise Certified Admin
Last Update May 31, 2026
Total Questions : 202
We are offering FREE SPLK-1003 Splunk exam questions. All you do is to just go and sign up. Give your details, prepare SPLK-1003 free exam questions and then go for complete pool of Splunk Enterprise Certified Admin test questions that will help you more.



A Splunk administrator has been tasked with developing a retention strategy to have frequently accessed data sets on SSD storage and to have older, less frequently accessed data on slower NAS storage. They have set a mount point for the NAS. Which parameter do they need to modify to set the path for the older, less frequently accessed data in indexes.conf?
Which layers are involved in Splunk configuration file layering? (select all that apply)
What is the difference between the two wildcards ... and - for the monitor stanza in inputs, conf?
Where can scripts for scripted inputs reside on the host file system? (select all that apply)
When using license pools, volume allocations apply to which Splunk components?
Which of the following is true regarding LDAP integration with Splunk Enterprise?
What options are available when creating custom roles? (select all that apply)
In a distributed environment, which Splunk component is used to distribute apps and configurations to the
other Splunk instances?
What is the correct example to redact a plain-text password from raw events?
The volume of data from collecting log files from 50 Linux servers and 200 Windows servers will require
multiple indexers. Following best practices, which types of Splunk component instances are needed?
The following stanzas in inputs. conf are currently being used by a deployment client:
[udp: //145.175.118.177:1001
Connection_host = dns
sourcetype = syslog
Which of the following statements is true of data that is received via this input?
Search heads in a company's European offices need to be able to search data in their New York offices. They also need to restrict access to certain indexers. What should be configured to allow this type of action?
Which feature of Splunk’s role configuration can be used to aggregate multiple roles intended for groups of
users?
Which authentication methods are natively supported within Splunk Enterprise? (select all that apply)
Which configuration files are used to transform raw data ingested by Splunk? (Choose all that apply.)
Assume a file is being monitored and the data was incorrectly indexed to an exclusive index. The index is
cleaned and now the data must be reindexed. What other index must be cleaned to reset the input checkpoint
information for that file?
What is the default character encoding used by Splunk during the input phase?
How is data handled by Splunk during the input phase of the data ingestion process?
During search time, which directory of configuration files has the highest precedence?
How would you configure your distsearch conf to allow you to run the search below? sourcetype=access_combined status=200 action=purchase splunk_setver_group=HOUSTON
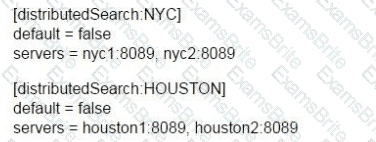
A)
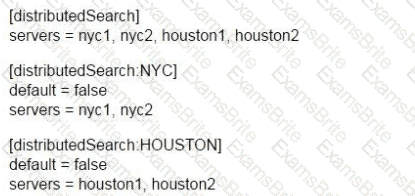
B)
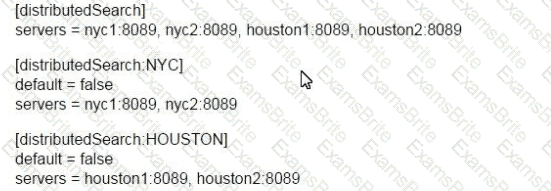
C)
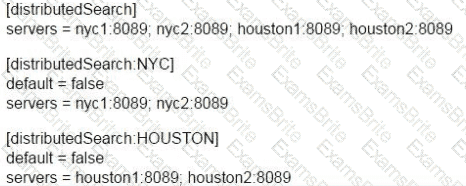
D)
The CLI command splunk add forward-server indexer:
which configuration file?
In inputs. conf, which stanza would mean Splunk was only reading one local file?
Which of the following CLI commands removes a search peer from Distributed Search?
Who provides the Application Secret, Integration, and Secret keys, as well as the API Hostname when setting
up Duo for Multi-Factor Authentication in Splunk Enterprise?
What is the importance of modifying Transparent Huge Pages (THP) and ulimit settings when installing Splunk Enterprise?
Which data pipeline phase is the last opportunity for defining event boundaries?
When using a directory monitor input, specific source type can be selectively overridden using which configuration file?
If an update is made to an attribute in inputs.conf on a universal forwarder, on which Splunk component
would the fishbucket need to be reset in order to reindex the data?
Which of the following statements describe deployment management? (select all that apply)
What type of data is counted against the Enterprise license at a fixed 150 bytes per event?
Which of the following apply to how distributed search works? (select all that apply)
Which of the following must be done to define user permissions when integrating Splunk with LDAP?
User role inheritance allows what to be inherited from the parent role? (select all that apply)
For single line event sourcetypes. it is most efficient to set SHOULD_linemerge to what value?
Given a forwarder with the following outputs.conf configuration:
[tcpout : mypartner]
Server = 145.188.183.184:9097
[tcpout : hfbank]
server = inputsl . mysplunkhfs . corp : 9997 , inputs2 . mysplunkhfs . corp : 9997
Which of the following is a true statement?
Windows can prevent a Splunk forwarder from reading open files. If files need to be read while they are being written to, what type of input stanza needs to be created?
This file has been manually created on a universal forwarder
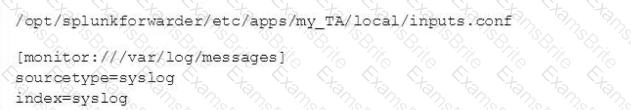
A new Splunk admin comes in and connects the universal forwarders to a deployment server and deploys the same app with a new
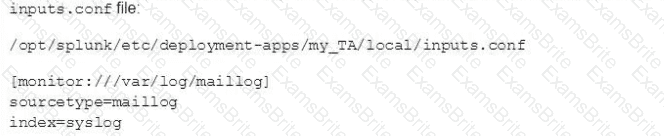
Which file is now monitored?
Within props. conf, which stanzas are valid for data modification? (select all that apply)
Using the CLI on the forwarder, how could the current forwarder to indexer configuration be viewed?
When configuring monitor inputs with whitelists or blacklists, what is the supported method of filtering the lists?
You update a props. conf file while Splunk is running. You do not restart Splunk and you run this command: splunk btoo1 props list —debug. What will the output be?
Which of the following statements accurately describes using SSL to secure the feed from a forwarder?
The following stanza is active in indexes.conf:
[cat_facts]
maxHotSpanSecs = 3600
frozenTimePeriodInSecs = 2630000
maxTota1DataSizeMB = 650000
All other related indexes.conf settings are default values.
If the event timestamp was 3739283 seconds ago, will it be searchable?
When working with an indexer cluster, what changes with the global precedence when comparing to a standalone deployment?
A user is assigned two roles with the following search filters. What is the user's applied search filter?