
Administering Information Security in Microsoft 365
Last Update May 31, 2026
Total Questions : 203
We are offering FREE SC-401 Microsoft exam questions. All you do is to just go and sign up. Give your details, prepare SC-401 free exam questions and then go for complete pool of Administering Information Security in Microsoft 365 test questions that will help you more.



Nate: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique
solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might
not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the
review screen.
You implement Microsoft 365 Endpoint data loss prevention (Endpoint DLP).
You have computers that run Windows 11 and have Microsoft 365 Apps installed. The computers are joined to a Microsoft Entra tenant.
You need to ensure that Endpoint DLP policies can protect content on the computers.
Solution: You onboard the computers to Microsoft Defender for Endpoint.
Does this meet the goal?
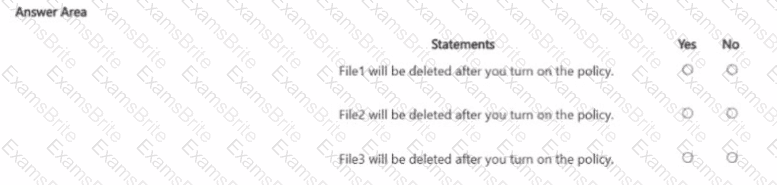
You have the files shown in the following table.
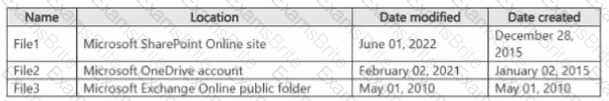
You configure a retention policy as shown > n the exhibit. (Click the Exhibit lab.)
The start of the retention period is based on when items are created. The current date is January 01. 207S.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
You need to meet the technical requirements for the creation of the sensitivity labels.
To which user or users must you assign the Sensitivity Label Administrator role?
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a Microsoft 365 tenant and 500 computers that run Windows 11. The computers are onboarded to Microsoft Purview.
You discover that a third-party application named Tailspin_scanner.exe accessed protected sensitive information on multiple computers. Tailspin_scanner.exe is installed locally on the computers.
You need to block Tailspin_scanner.exe from accessing sensitive documents without preventing the application from accessing other documents.
Solution: From Microsoft Defender for Cloud Apps, you create an app discovery policy.
Does this meet the goal?
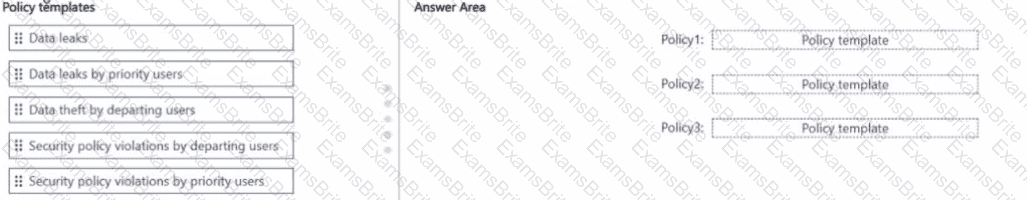
You have a Microsoft 36S ES subscription.
You need to create the Microsoft Purview insider risk management policies shown in the following table.
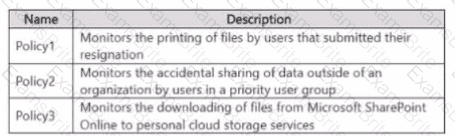
Which policy template should you use for each policy? To answer, drag the appropriate policy templates to the correct polices
Each template may be used once more than once or not at all. You may need to drag the split bar between panes or scroll to view..
You need to provide a user with the ability to view data loss prevention (DIP) alerts in the Microsoft Purview portal. The solution must use the principle of least privilege.
Which role should you assign to the user?
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You recently discovered that the developers at your company emailed Azure Storage Account keys in plain text to third parties.
You need to ensure that when Azure Storage Account keys are emailed, the emails are encrypted.
Solution: You configure a mail flow rule that matches a sensitive info type.
Does this meet the goal?
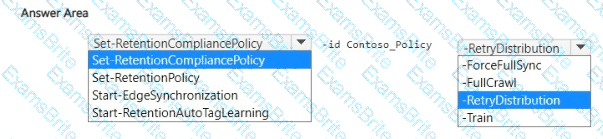
You create a retention label policy named Contoso_Policy that contains the following labels:
• 10 years then delete
• 5 years then delete
• Do not retain
Contoso.Policy is applied to content in Microsoft SharePoint Online sites.
After a couple of days, you discover the following messages on the Properties page of the label policy:
• Status: Off (Error)
• It ' s taking longer than expected to deploy the policy
You need to reinitiate the policy.
How should you complete the command? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft 36S subscription that contains the users shown in the following table.
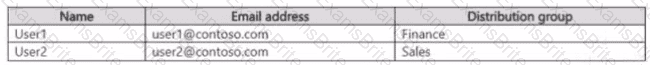
You create the data loss prevention (DLP) policies shown in the following table.
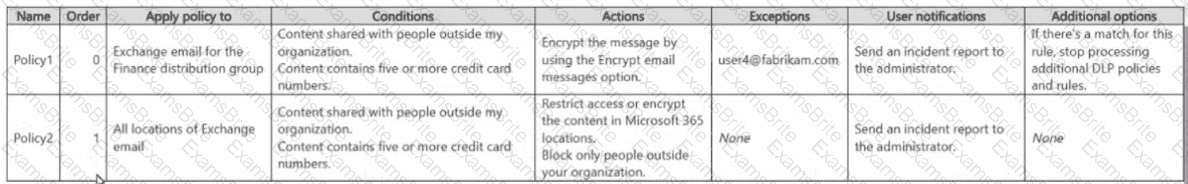
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
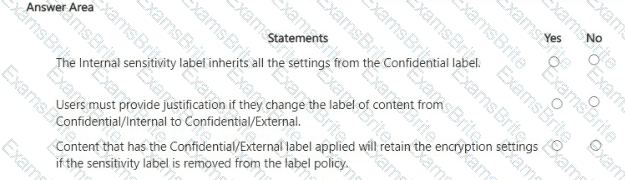
You have a Microsoft 365 E5 tenant.
You have sensitivity labels as shown in the Sensitivity Labels exhibit. (Click the Sensitivity Labels tab.)
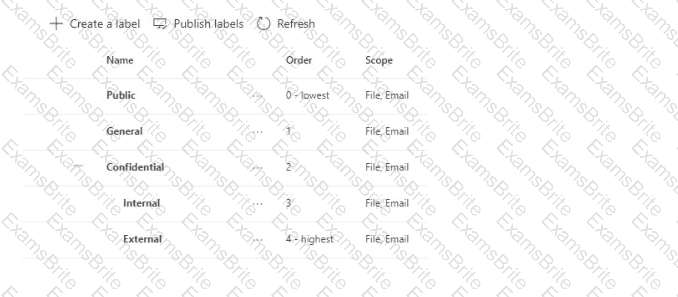
The Confidential/External sensitivity label is configured to encrypt files and emails when applied to content.
The sensitivity labels ate published as shown in the Published exhibit. (Click the Published tab.)
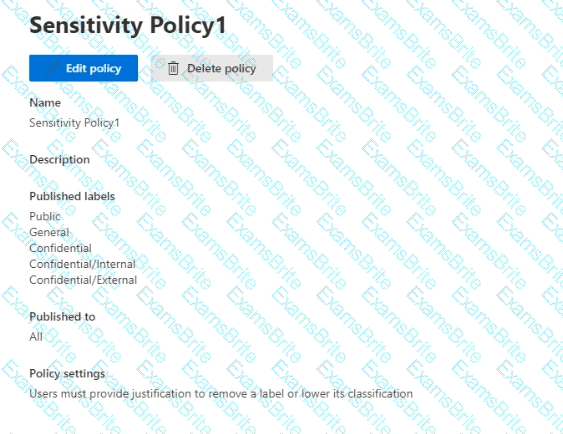
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 ES subscription.
You have a Microsoft SharePoint Online document library that contains Microsoft Word and Excel documents. The documents contain the following types of information:
• Credit card numbers
• Physical addresses in the UK
• National hearth service numbers from the UK
• Sensitive projects that contain the following words: Project Tailspin. Project Contoso, and Project falcon
You have email messages m Microsoft Exchange Online that contain the following information types:
• Credit card numbers
• User sign-in credentials
• National health service numbers from the UK
You plan to use sensitive information types (SITs) for compliance policies.
What is the minimum number of SITs required to classify all the information types?
You have a Microsoft 365 E5 subscription.
You plan to deploy Microsoft Purview Data Security Posture Management for Al (DSPM for Al) to protect company data that contains Personally Identifiable Information (Pll) from being shared with third-party generative Al tools.
You need to complete the prerequisites for the planned deployment.
Which two Microsoft Purview solutions should you use? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
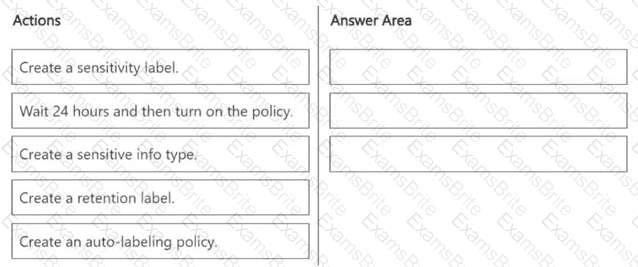
You need to meet the technical requirements for the Site1 documents.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
HOTSPOT
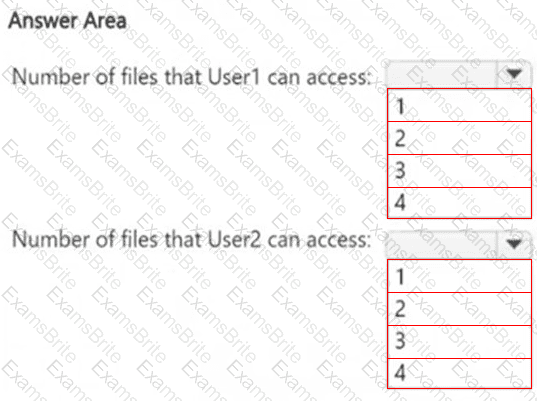
How many files in Site2 can User1 and User2 access after you turn on DLPpolicy1? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
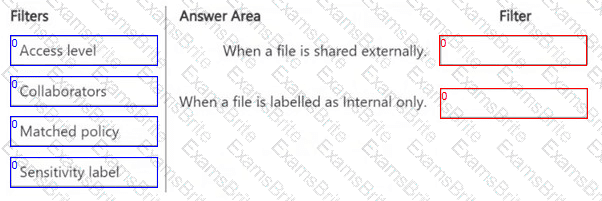
You have a Microsoft 365 E5 subscription that uses Microsoft Defender for Cloud Apps.
You plan to deploy a Defender for Cloud Apps file policy that will be triggered when the following conditions are met:
● A file is shared externally.
● A file is labeled as internal only.
Which filter should you use for each condition? To answer, drag the appropriate filters to the correct conditions. Each filter may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE : Each correct selection is worth one point.
You have a Microsoft 365 subscription.
You need to customize encrypted email for the subscription. The solution must meet the following requirements.
● Ensure that when an encrypted email is sent, the email includes the company logo.
● Minimize administrative effort.
Which PowerShell cmdlet should you run?
You have a Microsoft 365 E5 subscription.
You need to create a sensitivity label named Label1. The solution must ensure that users can use Microsoft 365 Copilot to summarize files that have Label1 applied.
Which permission should you select for Label1?
HOTSPOT
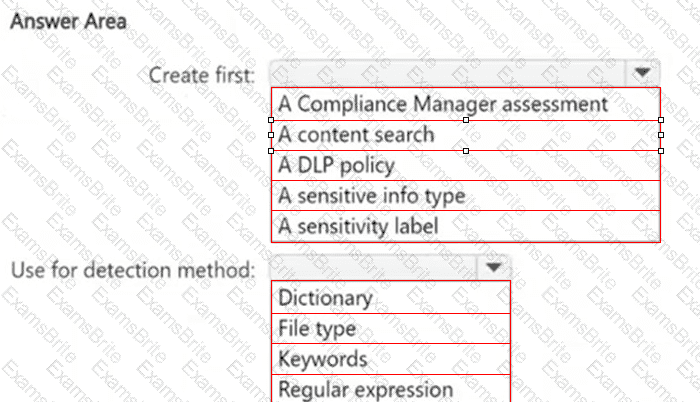
You need to meet the technical requirements for the confidential documents.
What should you create first, and what should you use for the detection method? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to meet the retention requirement for the users ' Microsoft 365 data.
What is the minimum number of retention policies required to achieve the goal?
HOTSPOT
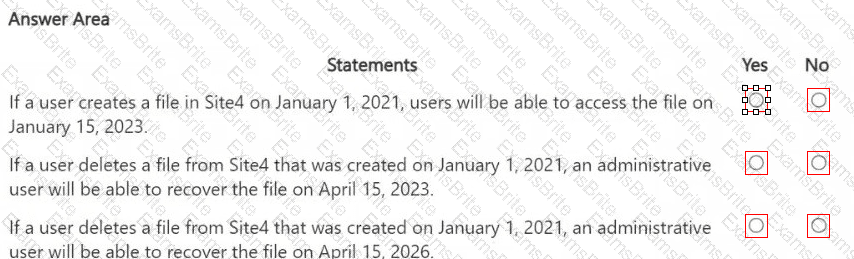
You are reviewing policies for the SharePoint Online environment.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
You need to test Microsoft Purview Advanced Message Encryption capabilities for your company. The test must verify the following information:
• The acquired default template names
• The encryption and decryption verification status
Which PowerShell cmdlet should you run?
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You recently discovered that the developers at your company emailed Azure Storage Account keys in plain text to third parties.
You need to ensure that when Azure Storage Account keys are emailed, the emails are encrypted.
Solution: You configure a mail flow rule that matches the text patterns.
Does this meet the goal?
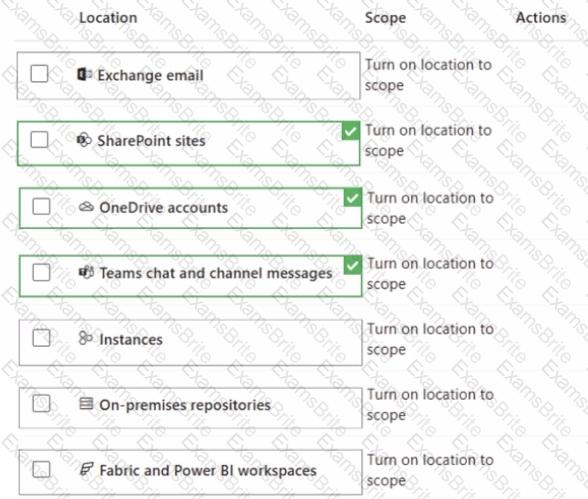
You have a Microsoft 365 tenant that uses Microsoft Teams.
You create a data loss prevention (DLP) policy to prevent Microsoft Teams users from sharing sensitive information. You need to identify which locations must be selected to meet the following requirements:
• Documents that contain sensitive information must not be shared inappropriately in Microsoft Teams.
• If a user attempts to share sensitive information during a Microsoft Teams chat session, the message must be deleted immediately.
Which three locations should you select? To answer, select the appropriate locations in the answer area
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 subscription.
Users have devices that run Windows 11.
You plan to create a Microsoft Purview insider risk management policy that will detect when a user performs the following actions:
● Deletes files that contain a sensitive information type (SIT) from their device
● Copies files that contain a SIT to a USB drive
● Prints files that contain a SIT
You need to prepare the environment to support the policy.
What should you do?
You have a Microsoft 365 E5 subscription that uses Microsoft Purview.
You create a communication compliance policy named Policy1 and select Detect Microsoft Copilot interactions.
Which two trainable classifiers will be added to Policy1 automatically? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a Microsoft 365 tenant and 500 computers that run Windows 11. The computers are onboarded to Microsoft Purview.
You discover that a third-party application named Tailspin_scanner.exe accessed protected sensitive information on multiple computers. Tailspin_scanner.exe is installed locally on the computers.
You need to block Tailspin_scanner.exe from accessing sensitive documents without preventing the application from accessing other documents.
Solution: From the Microsoft Defender for Cloud Apps, you mark the application as Unsanctioned.
Does this meet the goal?
You have a Microsoft 365 E5 subscription that contains a user named User1.
You need to ensure that all email messages that contain attachments are encrypted automatically by using Microsoft Purview Message Encryption.
What should you create?
You have a Microsoft 365 E5 subscription. The subscription contains a user named User1 and the sensitivity labels shown in the following table.
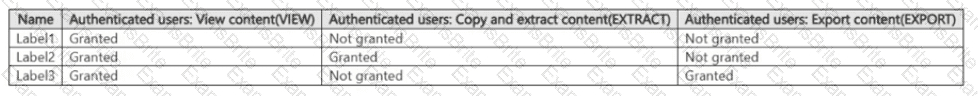
You publish the labels to User1.
The subscription contains the files shown in the following table.

Which files can Microsoft 365 Copilot summarize for User1?
You have a data loss prevention (DIP) policy that applies to the Devices location. The policy protects documents that contain United States passport numbers
Users report that they cannot upload documents to a travel management website because of the pokey.
You need to ensure that the users can upload the documents to the travel management website. The solution must prevent the protected content from being uploaded to other locations.
Which Microsoft 365 Endpoint data loss prevention (Endpoint DIP) setting should you configure?
You have a Microsoft 365 subscription.
You need to ensure that users can apply retention labels to individual documents in their Microsoft SharePoint libraries.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.