
Aruba Certified Network Security Professional Exam
Last Update May 31, 2026
Total Questions : 156
We are offering FREE HPE7-A02 HP exam questions. All you do is to just go and sign up. Give your details, prepare HPE7-A02 free exam questions and then go for complete pool of Aruba Certified Network Security Professional Exam test questions that will help you more.



A company wants to apply a standard configuration to all AOS-CX switch ports and have the ports dynamically adjust their configuration based on the identity of
the user or device that connects. They want to centralize configuration of the identity-based settings as much as possible.
What should you recommend?
A company requires a centralized audit trail for commands that managers enter on AOS-CX switches.
What can you set up on the switches to meet this requirement?
You have created this rule in an HPE Aruba Networking ClearPass Policy Manager (CPPM) service ' s enforcement policy: IF Authorization [Endpoints Repository]
Conflict EQUALS true THEN apply " quarantine_profile "
What information can help you determine whether you need to configure cluster-wide profiler parameters to ignore some conflicts?
The following firewall role is configured on HPE Aruba Networking Central-managed APs:
wlan access-rule employees
index 3
rule any any match 17 67 67 permit
rule any any match any 53 53 permit
rule 10 5 5.0 255.255 255.0 match any any any deny
rule 10.5 0.0 255.255 0.0 match 6 80 80 permit
rule 10.5 0.0 255.255.0.0 match 6 443 443 permit
rule 10.5.0.0 255.255.0.0 match any any any deny
rule any any match any any any permit
A client has authenticated and been assigned to the employees role. The client has IP address 10.2.2.2. Which correctly describes behavior in this policy?
A company has HPE Aruba Networking Central-managed APs. The company wants to block all clients connected through the APs from using YouTube.
Which steps should you take?
A company has AOS-CX switches and HPE Aruba Networking ClearPass Policy Manager (CPPM). The company wants switches to implement 802.1X
authentication to CPPM and download user roles.
What is one task that you must complete on the switches to support this use case?
A company wants you to integrate HPE Aruba Networking ClearPass Policy Manager (CPPM) with HPE Aruba Networking ClearPass Device Insight (CPDI).
What is one aspect of the integration that you should explain?
A company wants to turn on Wireless IDS/IPS infrastructure and client detection at the high level on HPE Aruba Networking APs. The company does not want to
enable any prevention settings.
What should you explain about HPE Aruba Networking recommendations?
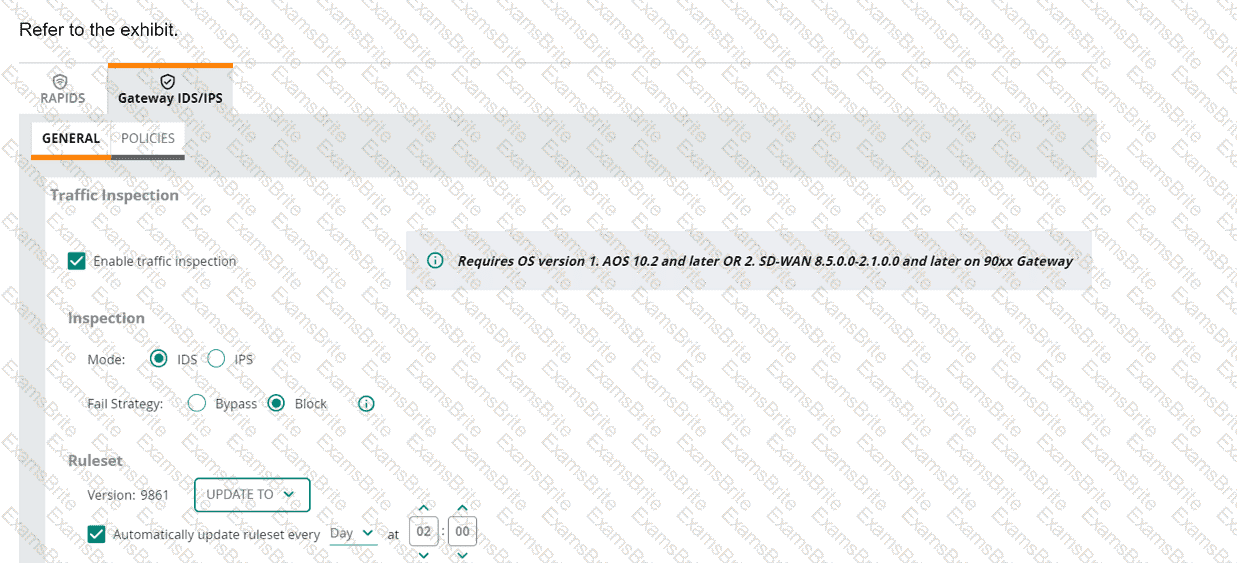
(Note that the HPE Aruba Networking Central interface shown here might look slightly different from what you see in your HPE Aruba Networking Central
interface as versions change; however, similar concepts continue to apply.)
An HPE Aruba Networking 9x00 gateway is part of an HPE Aruba Networking Central group that has the settings shown in the exhibit. What would cause the
gateway to drop traffic as part of its IDPS settings?
A company has HPE Aruba Networking infrastructure devices. The devices authenticate clients to HPE Aruba Networking ClearPass Policy Manager (CPPM). You want CPPM to track information about clients, such as their IP addresses and their network bandwidth utilization. What should you set up on the network infrastructure devices to help that happen?
A company lacks visibility into the many different types of user and loT devices deployed in its internal network, making it hard for the security team to address
those devices.
Which HPE Aruba Networking solution should you recommend to resolve this issue?
Refer to the exhibit.
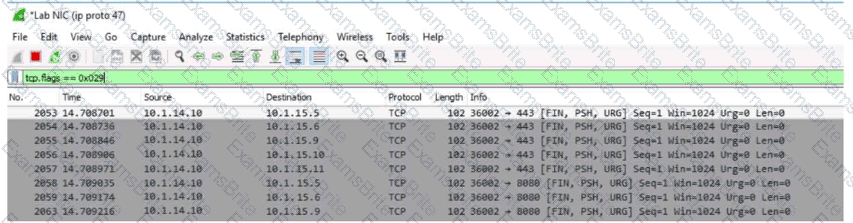
You are reviewing packets in Wireshark. The capture shows traffic from source IP address 10.1.14.10 to several destinations in the 10.1.15.0/24 network. The packets use TCP flags FIN, PSH, and URG together.
What can you interpret from the packets that you see here?
A company wants you to create a custom device fingerprint on CPPM with rules for profiling a group of specialized devices. What is one requirement?
A company wants to use HPE Aruba Networking ClearPass Onboard to issue certificates to BYOD devices. These certificates should be valid only for authenticating the company’s ClearPass cluster.
What type of Onboard CA should you set up?
Refer to the exhibit.
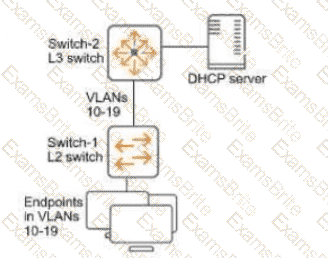
You have verified that AOS-CX Switch-1 has constructed an IP-to-MAC binding table in VLANs 10-19. Now you need to enable ARP inspection for the endpoint connected to Switch-1. What must you do first to prevent traffic disruption?
A company is using HPE Aruba Networking Central SD-WAN Orchestrator to establish a hub-spoke VPN between branch gateways (BGWs) at 1164 site and VPNCs at multiple data centers. What is part of the configuration that admins need to complete?
What is one use case for implementing user-based tunneling (UBT) on AOS-CX switches?
A company wants to implement Virtual Network based Tunneling (VNBT) on a particular group of users and assign those users to an overlay network with VNI
3000.
Assume that an AOS-CX switch is already set up to:
. Implement 802.1X to HPE Aruba Networking ClearPass Policy Manager (CPPM)
. Participate in an EVPN VXLAN solution that includes VNI 3000
Which setting should you configure in the users ' AOS-CX role to apply VNBT to them when they connect?
Refer to the exhibits.
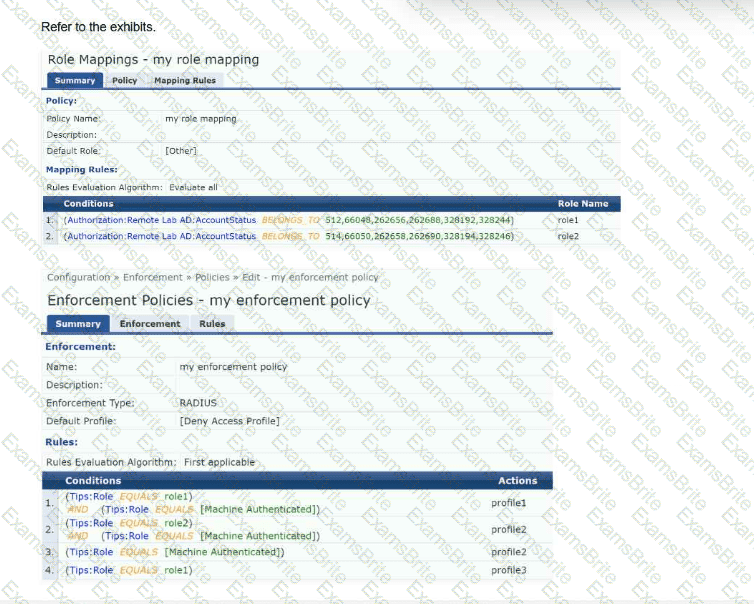
HPE Aruba Networking ClearPass Policy Manager (CPPM) is authenticating 802.1X clients using Active Directory as the source. CPPM has a custom attribute for AD that uses AccountStatus as userAccountControl .
Which enforcement profile does CPPM apply to a client that:
Succeeds in authenticating to an active AD user account: userAccountControl = 512
Does not succeed at authenticating as a computer
A company is using HPE Aruba Networking ClearPass Device Insight (CPDI) (the standalone application). You have identified a device, which is currently
classified as one type, but you want to classify it as a custom type. You also want to classify all devices with similar attributes as this type, both already-discovered
devices and new devices discovered later.
What should you do?
You are configuring the HPE Aruba Networking ClearPass Device Insight Integration settings on ClearPass Policy Manager (CPPM). For which use case should you set the ' Tag Updates Action " to " apply for all tag updates " ?
A company uses HPE Aruba Networking ClearPass Device Insight (CPDI) (the standalone application option). In the details for a generic device cluster, you see a
recommendation for " Windows 8/10 " with 70% accuracy.
What does this mean?
A company has HPE Aruba Networking APs, which authenticate users to HPE Aruba Networking ClearPass Policy Manager (CPPM).
What does HPE Aruba Networking recommend as the preferred method for assigning clients to a role on the AOS firewall?
A company needs you to integrate HPE Aruba Networking ClearPass Policy Manager (CPPM) with HPE Aruba Networking ClearPass Device Insight (CPDI). What is one task you should do to prepare?
A company is using HPE Aruba Networking ClearPass Device Insight (CPDI) (the standalone application). In the CPDI security settings, Security Analysis is On, the Data Source is ClearPass Device Insight, and Enable Posture Assessment is On. You see that a device has a Risk Score of 90.
What can you know from this information?
A company uses HPE Aruba Networking ClearPass Policy Manager (CPPM) as a TACACS+ server to authenticate managers on its AOS-CX switches. The
company wants CPPM to control which commands managers are allowed to enter. You see there is no field to enter these commands in ClearPass.
How do you start configuring the command list on CPPM?
A company has AOS-CX switches, which authenticate clients to HPE Aruba Networking ClearPass Policy Manager (CPPM). CPPM is set up to receive a variety of information about clients ' profile and posture. New information can mean that CPPM should change a client ' s enforcement profile. What should you set up on the switches to help the solution function correctly?
Which use case is fulfilled by applying a time range to a firewall rule on an AOS device?
A company has HPE Aruba Networking APs and AOS-CX switches. The APs bridge wireless traffic. They receive DHCP IP addresses on VLAN 18. Wireless users are assigned to VLAN 12.
The company wants the APs to start using 802.1X authentication on their switch ports. You are configuring the port-access role to which the APs are assigned after authentication.
What is one recommended setting for that role?
A company wants HPE Aruba Networking ClearPass Policy Manager (CPPM) to respond to Syslog messages from its Check Point firewall. You have added the
firewall as an event source and set up an event service. However, test Syslog messages are not triggering the expected actions.
What is one CPPM setting that you should check?
A company is implementing a client-to-site VPN based on tunnel-mode IPsec.
Which devices are responsible for the IPsec encapsulation?
A company has HPE Aruba Networking APs running AOS-10 and managed by HPE Aruba Networking Central. The company also has AOS-CX switches. The security team wants you to capture traffic from a particular wireless client. You should capture this client’s traffic over a 15-minute time period and then send the traffic to them in a PCAP file. What should you do?
You are setting up HPE Aruba Networking SSE. Which use case requires you to apply a non-default device posture in a rule?
What is a typical use case for using HPE Aruba Networking ClearPass Onboard to provision devices?
What is one benefit of integrating HPE Aruba Networking ClearPass Policy Manager (CPPM) with third-party solutions such as Mobility Device Management (MDM) and firewalls?
A company has HPE Aruba Networking APs managed by HPE Aruba Networking Central. You have set up a WLAN to enforce WPA3 with 802.1X authentication.
What happens if the client fails authentication?
Which issue can an HPE Aruba Networking Secure Web Gateway (SWG) solution help customers address?
You manage AOS-10 APs with HPE Aruba Networking Central. A role is configured on these APs with these rules (in order):
Allow UDP on port 67 to any destination
Allow any to network 10.1.4.0/23
Deny any to network 10.1.0.0/18 + log
Deny any to network 10.0.0.0/8
Allow any to any destination
You add this new rule immediately before rule 4:
Deny SSH to network 10.1.0.0/21 + denylist
After this change, what happens when a client assigned to this role sends SSH traffic to 10.1.7.12?
You are deploying a virtual Data Collector for use with HPE Aruba Networking ClearPass Device Insight (CPDI). You have identified VLAN 101 in the data center
as the VLAN to which the Data Collector should connect to receive its IP address and connect to HPE Aruba Networking Central.
Which Data Collector virtual ports should you tell the virtual admins to connect to VLAN 101?
A company has AOS-CX switches and HPE Aruba Networking ClearPass Policy Manager (CPPM). The company wants switches to implement 802.1X authentication to CPPM and download user roles. What is one task that you must complete on CPPM to support this use case?
HPE Aruba Networking ClearPass Device Insight (CPDI) could not classify some endpoints using system and user rules. Using machine learning, it did assign those endpoints to a cluster and discover a recommendation. In which of these circumstances does CPDI automatically classify the endpoints based on that recommendation?
A company is using HPE Aruba Networking ClearPass Policy Manager (CPPM) and HPE Aruba Networking ClearPass Device Insight (CPDI). CPDI and CPPM are integrated. The security staff wants you to show them a list of all devices that are contacting a specific known command-and-control center.
What should you do?
You are setting up policy rules in HPE Aruba Networking SSE. You want to create a single rule that permits users in a particular user group to access multiple applications. What is an easy way to meet this need?
An AOS-CX switch has been configured to implement UBT to two HPE Aruba Networking gateways that implement VRRP on the users ' VLAN. What correctly describes how the switch tunnels UBT users ' traffic to those gateways?
A company has AOS-CX switches managed by HPE Aruba Networking Central. The network infrastructure devices authenticate clients to HPE Aruba Networking ClearPass Policy Manager (CPPM), which is integrated with HPE Aruba Networking ClearPass Device Insight (CPDI). You have seen suspicious activity on a client connected to one of the switches. To investigate the client’s activity further, you need to know all of the IP addresses that it has used in the past two weeks.
Where can you find this information collected together?