
Certified in Planning and Inventory Management (CPIM 8.0)
Last Update May 31, 2026
Total Questions : 606
We are offering FREE CPIM-8.0 APICS exam questions. All you do is to just go and sign up. Give your details, prepare CPIM-8.0 free exam questions and then go for complete pool of Certified in Planning and Inventory Management (CPIM 8.0) test questions that will help you more.



The question below is based on the following information:
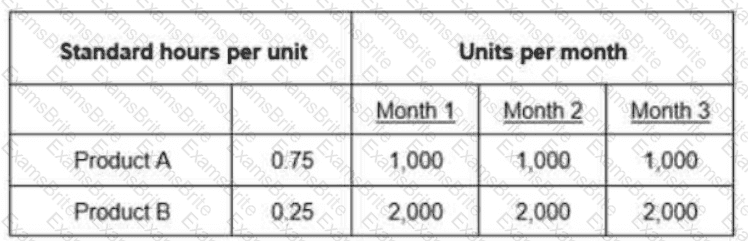
Work Center 1 has an available capacity of 1,200 hours per month. Which of the following amounts represents the cumulative difference between the required capacity and the available capacity of Months 1 through 3?
A large organization wants to implement a vulnerability management system in its internal network. A security professional has been hired to set up a vulnerability scanner on premises and to execute the scans periodically. Which of the following should be the FIRST action performed by the security professional?
The demand for an item has increasing forecast error, whereas all other factors remain constant. Which of the following remains constant while maintaining the same customer service level?
In which cloud computing model is Identify And Access Management (IAM) the responsibility of a service provider?
An organization is implementing improvements to secure the Software Development Life Cycle (SDLC). When should defensive three modeling occur?
An organization has been the subject of increasingly sophisticated phishing campaigns in recent months and has detected unauthorized access attempts against its Virtual Private Network (VPN) concentrators. Which of the following implementations would have the GREATEST impact on reducing the risk of credential compromise?
Which of the following data is needed to determine gross requirements when conducting distribution requirements planning (DRP)?
Which of the following methods places a replenishment order when the quantity on hand falls below a predetermined level?
An infrastructure team is setting up a wireless network for employees at a new location of the organization that is located near a very busy city transport hub. Which should be the MOST important antenna consideration with regard to securing the wireless network for the infrastructure team?
An appropriate performance measure for sales and operations planning (S & OP) would be the variance between:
An organization implemented a threat modeling program focusing on key assets. However, after a short time it became clear that the organization was having difficulty executing the threat modeling program.
Which approach will MOST likely have been easier to execute?
Which of the following Internet Protocol Security (IPSec) components provides the MOST confidentiality for the information that is being transmitted?
The question below is based on the following standard and actual data of a production order
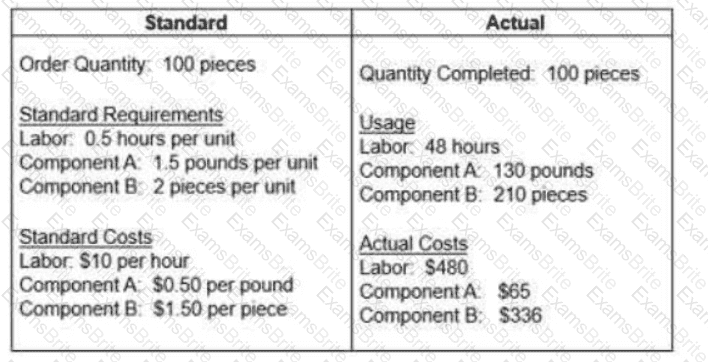
Which of the following statements about variances is true?
An organization wants to implement Zero Trust (ZT). The Information Technology (IT) department is already using Multi-Factor Authentication (MFA) and Identity and Access Management (IAM). Which of the following would be the BEST solution for the organization to implement in order to have a ZT network?
In the context of mobile device security, which of the following BEST describes why a walled garden should be implemented?
The Business Continuity Plan (BCP) has multiple components. The information security plan portion must prioritize its efforts. Which 3 aspects of information security MUST be prioritized?
An agency has the requirement to establish a direct data connection with another organization for the purpose of exchanging data between the agency and organization systems. There is a requirement for a formal agreement between the agency and organization. Which source of standards can the system owners use to define the roles and responsibilities along with details for the technical and security requirements?
An organization is opening a new data center and is looking for a facilities security officer to provide best practices for the site and facility design. The two major requirements for this organization are not to attract undue attention and avoid proximity to potentially hazardous sites.
What site selection considerations do these requirements BEST fall under when deciding on the location for a facility?
Which of the following categories of web services testing describes correctness testing of web service security functionality?
An organization is planning to streamline its Identity and Access Management (IAM) processes and platform. The executive team mandated a compact platform to efficiently manage identities for internal and third-party services access. What is the BEST platform choice?
Which security concept states that a subject (user, application, or asset) be given only the access needed to complete a task?
One of the benefits of Integrating a poka-yoke into the production process is that it can be used to:
Which of the following MUST be in place for security to be effective in an organization?
Which Open Systems Interconnection (OSI) layer is concerned with Denial-Of-Service (DoS) SYN flood attacks?
What can help a security professional assess and mitigate vulnerabilities of an embedded device?
Which of the following is a methodology for threat modeling in application?
An organization has received the results of their network security risk assessment. What is the BEST course of action for the organization to take in response to the analyzed report findings?
A recent email-based malware breakout caused a significant volume of traffic and password spam account lockouts for an organization. Which BEST identifies compromised devices?
An attacker wants to decrypt a message and has no knowledge of what may have been in the original message. The attacker chooses to use an attack that will exhaust the keyspace in order to decrypt the message. What type of cryptanalytic attack is the attacker using?
A company is having trouble with raw material deliveries and has decided to develop a supplier certification program. The certification process most appropriately would start with which of the following suppliers?
Which technology is BEST suited to establish a secure communications link between an individual’s home office and the organization’s Local Area Network (LAN)?
An organization’s external auditors have issued a management letter identifying significant deficiencies related to the effectiveness of the previous year’s global access certification. The organization wants to move from a department-based access control system to a Role-Based Access Control (RBAC) system. In addition to quickly and securely provisioning users by granting membership into predefined and approved roles, which of these presents the BEST reason to do so?
Which of the following statements is true about total productive maintenance (TPM)?
The Data Loss Prevention (DLP) team in a major financial institution discovered network traffic that involved movement of sensitive material to a Cloud Service Provider (CSP). What action should be taken FIRST in this situation?
Which of the following capabilities BEST distinguishes a Next-Generation Firewall (NGFW) from a traditional firewall?
Which of the following is PRIMARILY responsible for deciding the classification of data in an organization?
Which of the following provides that redundancy and failover capabilities are built into a system to maximize its uptime?
Which of the following BEST describes web service security conformance testing as it relates to web services security testing?
A security engineer is implementing an authentication system for a new web application. The authentication requirements include the ability for a server to authenticate the client and for the client to authenticate the server. Which of the following choices BEST supports this requirement?
Which of the following measurements indicates there may be bias In the forecast model?
A hot Disaster Recovery (DR) data center is the victim of a data breach. The hackers are able to access and copy 10GB of clear text confidential information. Which of the following could have decreased the amount of exposure from this data breach?
Which of the below represents the GREATEST cloud-specific policy and organizational risk?
Disaster Recovery (DR) training plan outcomes should have which KEY quality?
Organization A provides scalable Information Technology (IT) infrastructure while Organization B provides security services to customers via Software as a Service (SaaS) model. Which document is used to express a set of intended actions between the organizations with respect to meeting the customers’ needs?
A team is tasked with developing new email encryption software. To ensure security, what will be the PRIMARY focus during the initial phase of development?
Which of the following MUST be checked during the validation of software verification capabilities?
A failure mode and effects analysis (FMEA) could be used for which of the following activities?
A third-party vendor is procured to conduct a non-financial audit. Which report evaluates the effectiveness of the controls?
A work center has 3 machines that are all run at the same time with a single worker. The work center has an efficiency of 75% and a utilization of 100%. What is the work center ' s capacity in standard hours for an 8-hour shift?
A security team leader needs to communicate the value of the security program. As the security team leader determines the return on security investments, what is the MOST important aspect to incorporate?
An organization has identified that an individual has failed to adhere to a given standard set by the organization. Based on the needs of the organization, it was decided that an exception process will be created. What is the PRIMARY benefit of establishing an exception process?
A furniture manufacturer using material requirements planning (MRP) and lean manufacturing has changed the bills of material (BOMs) for all chests by making drawers into phantom assemblies. Which of the following outcomes would likely result from this change?
The security department was notified about vulnerabilities regarding users ' identity verification in a web application. Which of the following vulnerabilities is the security professional MOST likely to test?
Which of the following statements correctly describes the relationship between the strategic plan and the business plan?
In order for an organization to mature their data governance processes to ensure compliance, they have created a data classification matrix.
What are the next BEST activities to build on this completed work?
Which of the following conditions is most likely to result in planned production that is greater than the total demand over the sales and operations planning (S & OP) horizon for a product family that is
made to stock?
A healthcare organization is preparing an exercise test plan of its Disaster Recovery Plan (DRP) for the Electronic Medical Record (EMR) application. The Business Continuity (BC) analyst is reviewing the requirements of the DRP. The EMR must provide basic charting services within 4 hours, must not lose more than 15 minutes of data, and must be fully functional within 12 hours. At the completion of the exercise, the analyst is preparing a lessons learned report and notes that the EMR was available after 3 hours and 25 minutes of data was lost. Which PRIMARY requirement needs to be addressed because of the exercise?
Which of the following incorporates design techniques promoted by Crime Prevention Through Environmental Design (CPTED)?
Capacity requirements planning (CRP) is applicable primarily In companies operating In an environment where:
A Generic Routing Encapsulation (GRE) tunnel moves data across a third-party Internet Protocol (IP) network. What is the risk of using GRE tunnels?
The time spent In queue by a specific manufacturing job is determined by which of the following factors related to the order?
A multinational organization acquires a subsidiary. The acquisition results in the need to integrate a large population of new users into the organization ' s corporate cloud. What is the MAIN benefit of the organization ' s Federated Identity Management (FIM) system to address the need?
What is a malicious activity that overwhelms a Wireless Access Point (WAP)?
A new organization building is being designed and the security manager has been asked for input on needed security requirements. Which of the following controls are MOST applicable to this scenario?
The primary consideration In maintenance, repair, and operating (MRO) supply systems typically is:
An organization has decided to give decommissioned computers to a school in a developing country. The company data handling policy prohibits the storage of confidential and sensitive data. What would be the BEST technique to use to avoid data remanence, and to minimize the operational burden for the inheriting school?
Access Control Lists (ACL), protection bits, and file passwords are typical examples of which of the following access control methods?
An organization ' s security policy requires sensitive information to be protected when being transmitted to external sources via would be the BEST security solution to choose?
Which of the following BEST defines whether an organization can consider an alternate location during a contingency?
A newly hired Chief Information Security Officer (CISO) is now responsible to build a third-party assurance for their organization. When assessing a third-party, which of the following questions needs to be answered?
Improvements in an Input/output control (I/O control) system will most likely lead to:
An information security professional has been tasked with remediating vulnerabilities identified during a recent penetration test. Which of the following sections of the penetration results report would be MOST preferable to remediate hosts one at a time?
After a recent cybersecurity incident, a manufacturing organization is interested in further hardening its Identity and Access Management (IAM) solution. Knowing that the organization limits the use of personal devices in the facility, which could BEST be implemented to enhance the manufacturing organization ' s IAM solution?
During an onsite audit, an assessor inspected an organization’s asset decommission practice. Which of the following would MOST likely be a finding from a security point of view?
Which of the following regarding authentication protocols is a PRIMARY consideration when designing an authentication and key management system?
Which of the following MUST exist for an activity to be considered an audit?
To ensure the quality of its newly developed software, an organization is aiming to deploy an automated testing tool that validates the source code. What type of testing BEST supports this capability?
The planned channels of Inventory disbursement from one or more sources to field warehouses are known as:
An organization is aiming to be System and Organization Controls (SOC) 2 certified by an audit organization to demonstrate its security and availability maturity to its sub service organizations. Which type of audit does this engagement BEST describe?
An information security auditor is creating an audit program to assess endpoint security controls for portable storage media movement. Which type of control will MOST likely be part of the program?
In a large organization, the average time for a new user to receive access is seven days. Which of the following is the BEST enabler to shorten this time?
The development team wants new commercial software to Integrate into the current systems. What steps can the security office take to ensure the software has no vulnerabilities?
A company decided not to pursue a business opportunity In a foreign market due to political Instability and currency fluctuations. Which risk control strategy did this business utilize?
An information security professional is enhancing the organization ' s existing information security awareness program through educational posters. Which of the following is the MOST effective location for poster placement?
A security engineer must address resource sharing between various applications without adding physical hardware to the environment. Which secure design principle is used to BEST segregate applications?
As the organization requires user friendly access to a new web-based application, a software developer decides to implement Single Sign-On (SSO). The developer uses the de-facto standard for web-based applications and the implementation includes the use of a JavaScript Object Notation (JSON) web token. With this information, which is the BEST way for the software developer to establish SSO capability?
Objective security metrics tend to be easier to gather, easier to interpret, and easier to include in reports to management.
What is the BEST objective metric for the effectiveness of a security awareness training?
An organization has a requirement that all documents must be auditable and that the original is never modified once created. When designing the system, what security model MUST be implemented in order to meet this requirement?
Which of the following is a threat modeling methodology used for accessing threats against applications and Operating Systems (OS)?
When designing a production cell, which of the following items would be the most important consideration?
A customer of a financial Institution denies that a transaction occurred. Which of the following is used to provide evidence evidence that the customer performed the transaction?
Which of the following prioritization rules will have the greatest impact In reducing the number of orders In queue?
In a rapidly changing business environment, a primary advantage of an effective customer relationship management (CRM) program is:
Which of the following is an access control method that organizations can use to prevent unauthorized access?
Which of the following techniques is BEST suited to preserve the confidentiality of a system’s data?
An organization uses an external Identity Provider (IdP) to secure internal, external, or third-party applications. Which of the following is the GREATEST risk to the organization?
An information system containing Protected Health Information (PHI) will be accessed by doctors, nurses, and others working in a hospital. The same application will be used by staff in the pharmacy department only for dispensing prescribed medication. Additionally, patients can log in to view medical history. The system owner needs to propose an access control model that considers environment, situation, compliance, and security policies while dynamically granting the required level of access. Which access control model is the MOST suitable?
An organization recently created a new accounting department, and that department is critical in the event of a disaster for the operations to continue. Which steps should the organization take to create a Business Continuity Plan (BCP)?
Typically, rough-cut capacity planning (RCCP) in a job shop environment would review which of the following work centers to determine the ability to execute the plan?
A Structured Query Language (SQL) database is hosted on a hardened, secure server. All unused ports are locked down, but external connections from untrusted networks are still required to be allowed through. What is the BEST way to ensure transactions to/from this server remain secure?
A security engineer is responsible for verifying software reliability prior to commercial deployment. Which of the following factor would BEST be verified to ensure that the software stays reliable?
An advantage of applying ABC classification to a firm ' s replenishment items is that:
An organization is looking to integrate security concepts into the code development process early in development to detect issues before the software is launched. Which advantage does the organization gain from using Static Application Security Testing (SAST) techniques versus dynamic application security testing techniques?
A financial services organization wants to deploy a wireless network. Which of the following is the WEAKEST option for ensuring a secure network?
A security professional is accessing an organization-issued laptop using biometrics to remotely log into a network resource. Which type of authentication method is described in this scenario?
Which of the following BEST describes how an Application Programming Interface (API) gateway fits into an application architecture?
An effective approach to projecting requirements for materials with long lead times Includes which of the following options?
An organization is considering options to outsource their Information Technology (IT) operations. Although they do not sell anything on the Internet, they have a strong requirement in uptime of their application. After the offerings received by the Cloud Service Provider (CSP), the IT manager decided it was mandatory to develop processes to continue operations without access to community or public cloud-based applications. Which of the following arguments MOST likely led the IT manager to make this decision?
Increased use of third-party logistics (3PL) services is likely to have which of the following effects on a firm ' s balance sheet?
Which of the following tactics can be employed effectively to reduce appraisal quality costs?
An Information Technology (IT) professional is seeking a control objective framework that is widely accepted around the world and focuses specifically on information security controls. Which of the following frameworks BEST meets this need?
Which of the following statements is an advantage of a fourth-party logistics (4PL) provider?
Which of the following BEST characterizes the operational benefit of using immutable workloads when working on a cloud-based project?
Which of the following data elements is required for a manufacturing routing?
An information system security manager is tasked with properly applying risk management principle to their cloud information system as outlined by the National Institute of Standards and Technology (NIST).
Which of the following is the INITIAL step?
An organization is considering options to outsource their Information Technology (IT) operations. Although they do not sell anything on the Internet, they have a strong requirement in uptime of their application. After evaluating the offerings received by the Cloud Service Provider (CSP), the IT manager decided it was mandatory to develop processes to continue operations without access to community or public cloud-based applications. Which of the following arguments MOST likely led the IT manager to make this decision?
An advertising agency is working on a campaign for a prospective client. Competitors are working on a similar campaign and are interested in knowing what the firm has designed. What should the advertising agency do to BEST ensure intellectual property does not leave the organization?
Which of the following is the workflow of the identity and access provisioning lifecycle?
An organization has deployed an Identity And Access Management (IAM) tool and is expanding their information governance program. Which of the following would BEST be included in the governance for IAM?
Which of the following threats MUST be included while conducting threat modeling for a Cloud Service Provider (CSP)?
In a Discretionary Access Control (DAC) model, how is access to resources managed?
An organization currently has a network with 55,000 unique Internet Protocol (IP) addresses in their private Internet Protocol version 4 (IPv4) network range and has acquired another organization and must integrate their 25,000 endpoints with the existing, flat network topology. If subnetting is not implemented, which network class is implied for the organization’s resulting private network segment?
A security engineer has determined the need to implement preventative controls into their Wireless Local Area Network (WLAN) for added protection. Which preventative control provides the MOST security?
Which of the following factors typically would distort a sales forecast that is based solely on shipment history?
When an organization is recruiting for roles within the organization, at which stage of the employee life cycle are termination procedures incorporated?
Which approach will BEST mitigate risks associated with root user access while maintaining system functionality?
Which of the following are compromised in an untrusted network using public key cryptography when a digitally signed message is modified without being detected?
Company A has acquired Company B. Company A has decided to start a project to convert Company B ' s enterprise resource planning (ERP) software to the same ERP software that Company A uses. What is a likely reason for this decision?
What resources does a respondent have when contesting disciplinary action taken by the ISC2 Board of Directors?
Which of the following BEST represents a security benefit of Software-Defined Networking (SDN)?
Which of the following controls should a financial Institution have in place in order to prevent a trader from both entering and executing a trade?
An organization experienced multiple compromises of endpoints, leading to breaches of systems and data. In updating its strategy to defend against these threats, which of the following BEST considers the organization’s needs?
A security practitioner notices that workforce members retain access to information systems after transferring to new roles within the organization, which could lead to unauthorized changes to the information systems.
This is a direct violation of which common security model?
An organization co-locates three divisions and merges them into one network infrastructure. Prior to the merge, the network manager issued devices to employees for remote login. What security concept should be observed to provide security when a device joins the network or when a client makes an Application Programming Interface (API) call?
Which of the following actions hinders the transition from a push system to a pull system?
Which of the following production activity control (PAC) techniques focuses on optimizing output?
What is the following is the MAIN reason why hot-spot usually adopt open security mode in wireless networks?
The define, measure, analyze, improve, control (DMAIC) process is an effective method to understand and improve business processes because it begins with a:
An organization is concerned that if an employee’s mobile device is lost or stolen and does not reconnect to the carrier network, the data on the device may still be at risk. Consequently, the organization has implemented a control on all mobile devices to require an eight-character passcode for unlock and login. What should happen after multiple incorrect passcode attempts?
Following the go-live of a new financial software, an organization allowed the Information Technology (IT) officer to maintain all rights and access permissions to help the organization staff should they have challenges in their day-to-day work. What is the BEST way to categorize the situation?
A vendor has been awarded a contract to supply key business software. The vendor has declined all requests to have its security controls audited by customers. The organization insists the product must go live within 30 days. However, the security team is reluctant to allow the project to go live. What is the organization ' s BEST next step?
An organization provides customer call center operations for major financial services organizations around the world. As part of a long-term strategy, the organization plans to add healthcare clients to the portfolio. In preparation for contract negotiations with new clients, to which cybersecurity framework(s) should the security team ensure the organization adhere?
An organization’s computer incident response team PRIMARILY responds to which type of control?
Which of the following may authorize an organization to monitor an employee’s company computer and phone usage?
What FIRST step should a newly appointed Data Protection Officer (DPO) take to develop an organization ' s regulatory compliance policy?
Which of the following design considerations would offer the BEST protection against unauthorized access to the facility?
Which assessing whether real-world threats to the security of an application have been mitigated, what is MOST effective source to confirm that sufficient security controls are in place for both end users and customers?
Which of the following BEST effective when protecting against insider threats?
Labor3 people
Work hours10 hours per day
Days4 days per week
Meetings with work area employees1/2 hour per day
Work area efficiency85%
Given the information above, what is the weekly theoretical capacity of this work area in hours?
A product manager wishes to store sensitive development data using a cloud storage vendor while maintaining exclusive control over passwords and encryption credentials. What is the BEST method for meeting these requirements?
A software development vendor wants to test the Application Programming Interface (API). The testers use and manipulate data to identify the various states of the application behavior. What is the kind of testing that is being used?
In Company XYZ, transaction-costing capability has been Integrated into the shop floor reporting system. A batch of 20 units was started in production. At the fourth operation, 20 units are reported as complete. At the fifth operation, 25 units are reported as complete. When all operations are complete, 20 units are checked into the stockroom. If the error at the fifth operation is undetected, which of the following conditions will be true?
Which of the following concepts MOST accurately refers to an organization ' s ability to fully understand the health of the data in its system at every stage of the lifecycle?
When a third-party needs to receive privileged information, which of the following would be the BEST to
transport the data?
Which authentication method is used by an email server to verify that a sender’s Internet Protocol (IP) address is authorized to send messages by the sending domain?
A warehouse manager assigns orders to warehouse personnel grouped by where the goods are stored. This type of picking is called a(n):
The primary outcome of frequent replenishments in a distribution requirements planning (DRP) system is that:
An external audit is conducted on an organization ' s cloud Information Technology (IT) infrastructure. This organization has been using cloud IT services for several years, but its use is not regulated in any way by the organization and security audits have never been conducted in the past. Which task will be the MOST challenging to conduct an effective security audit?
Which if the following is the FIRST control step in provisioning user rights and privileges?
Endpoint security needs to be established after an organization procured 1,000 industrial Internet Of Things (IoT) sensors. Which of the following challenges are the security engineers MOST likely to face?
Which of the following is the GREATEST threat for a Border Gateway Protocol (BGP) deployment on the internet?
A systems engineer has been tasked by management to provide a recommendation with a prioritized, focused set of actions to help the organization stop high-risk cyber attacks and ensure data security. What should the systems engineer recommend the organization use to accomplish this?
What is the BEST protection method to ensure that an unauthorized entry attempt would fail when securing highly sensitive areas?
A security consultant is recommending the implementation of a security-focused Configuration Management (CM) process in an organization. What would be the BEST benefit the security consultant would include in the recommendation?