
Cisco Certified Design Expert (CCDE v3.1)
Last Update May 30, 2026
Total Questions : 503
We are offering FREE 400-007 Cisco exam questions. All you do is to just go and sign up. Give your details, prepare 400-007 free exam questions and then go for complete pool of Cisco Certified Design Expert (CCDE v3.1) test questions that will help you more.



While reviewing an existing network design, you are discussing the characteristics of different STP versions. Which protocol minimizes unicast flooding during a Topology Change Notification in a Layer 2 switched network with many VLANs?
Which two statements describe network automation and network orchestration? (Choose two.)
Company XYZ has 30 sites using MPLS L3 VPN and is concerned about data integrity. They want a centralized configuration model and minimal overhead. Which technology can be used?
An enterprise requires MPLS-connected branches to access cloud-based Microsoft 365 services over an SD-WAN solution. Internet access is available only at dual regional hub sites that are connected to the MPLS network. Which connectivity method provides an optimum access method to the cloud-based services if one ISP suffers loss or latency?
As network designer, which option is your main concern with regards to virtualizing multiple network zones into a single hardware device?
A large enterprise cloud design team is evaluating cloud consumption models. What is an example of a typical PaaS limitation or concern?
What is a disadvantage of the traditional three-tier architecture model when east-west traffic between different pods must go through the distribution and core layers?
A European national bank considers migrating its on-premises systems to a private cloud offering in a non-European location to significantly reduce IT costs. What is a primary factor prior to migration?
A product manufacturing organization is integrating cloud services into their IT solution. The IT team is working on the preparation phase of the implementation approach, which includes the Define Strategy step. This step defines the scope of IT, the application, and the service. What is one topic that should be considered in the Define Strategy step?
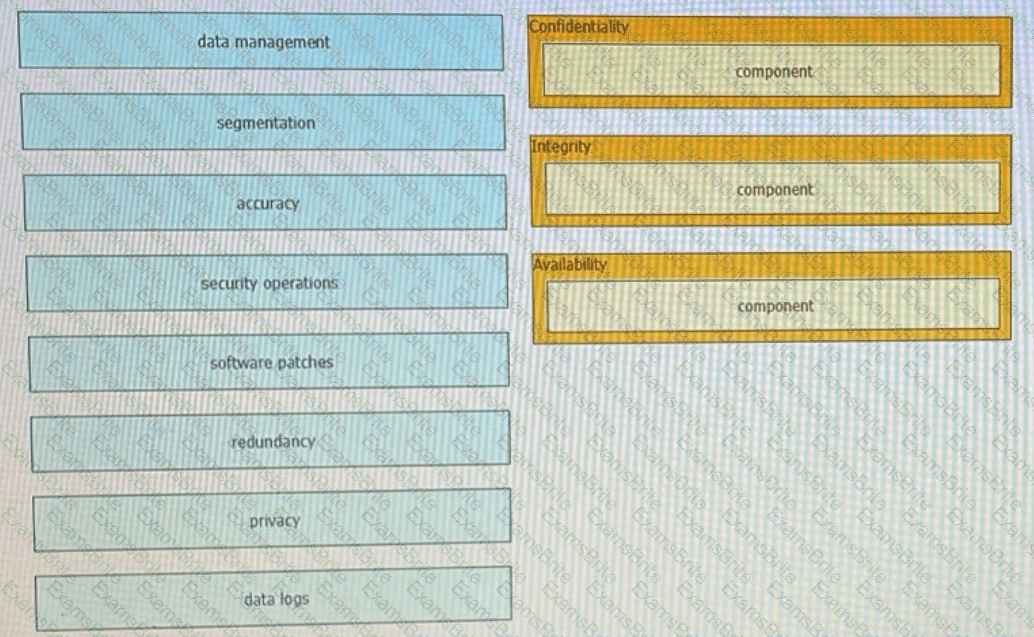
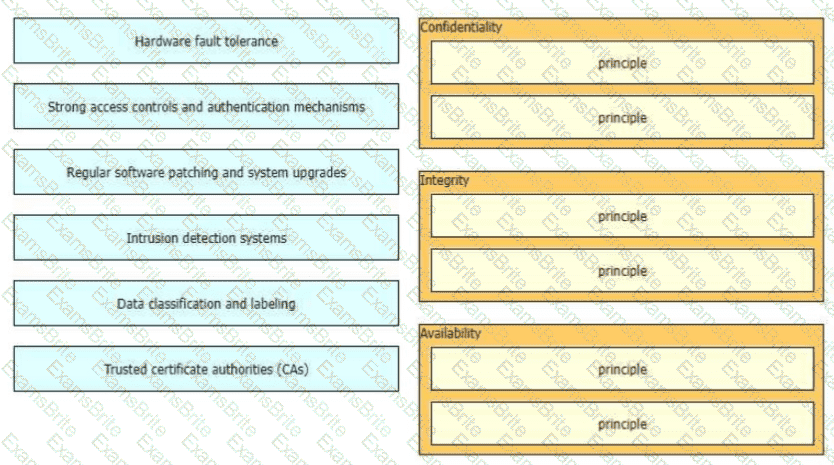
Drag lhe components that are part of the CIA triad to the correct target on the right. Not all components are used.
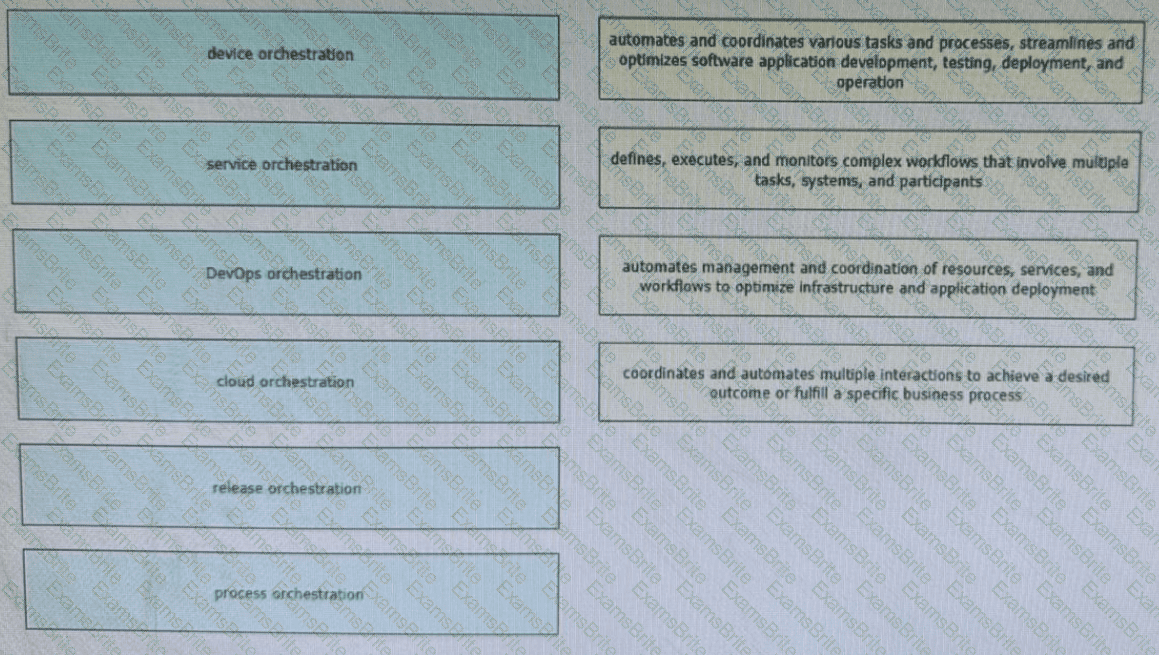
Network orchestration enables network administrators to focus on strategic initiatives, innovation, and value-added tasks rather than spending time on manual and repetitive network management activities. Drag and drop the orchestration types from the left onto the corresponding functions on the right. Not all options are used.
Which two control plane policer designs must be considered to achieve high availability? (Choose two.)
What is the primary benefit for an organization that dynamically can expand their private cloud capacity by allocating additional compute and/or storage resources using a third-party service provider or partner?
Refer to the exhibit.
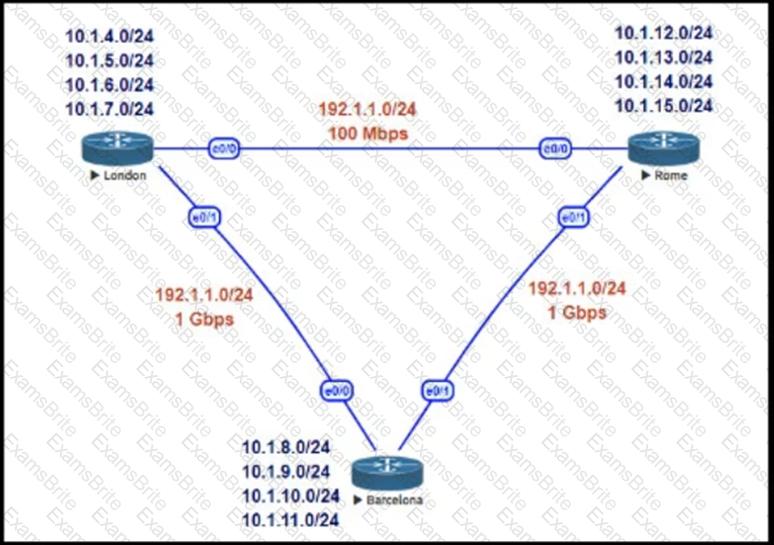
This network is running EIGRP as the routing protocol and the internal networks are being advertised in EIGRP. Based on the link speeds, all traffic between London and Rome is getting propagated via Barcelona and the direct link between London and Rome is not being utilized under normal working circumstances. The EIGRP design should allow for efficiency in the routing table by minimizing the routes being exchanged. The link between London and Rome should be utilized for specific routes. Which two steps accomplish this task? (Choose two.)
You are designing a network for a branch office. In order to improve convergence time, you are required to use the BFD feature. Which four routing protocols can you use to facilitate this? (Choose four.)
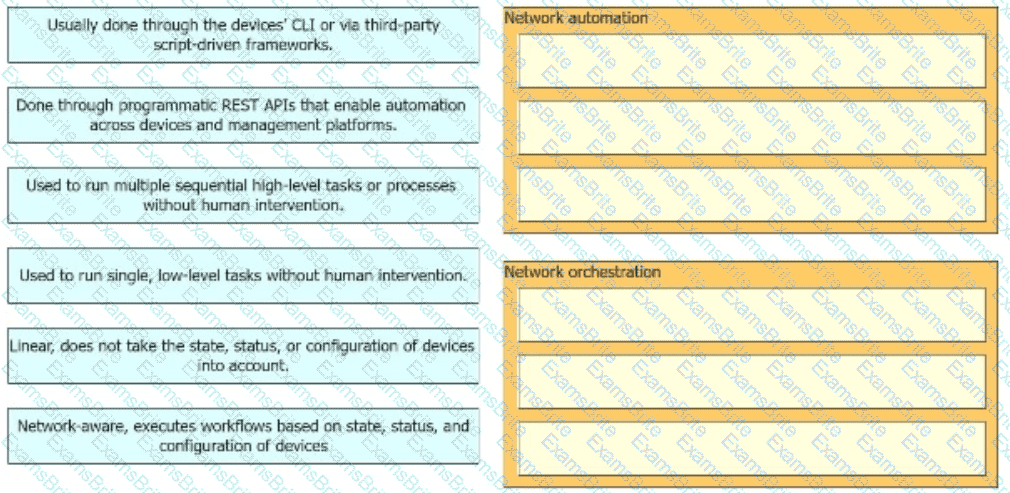
Drag and drop the high-level descriptions of network automation and network orchestration on the left to the corresponding category on the right in no particular order.
Refer to the exhibit.
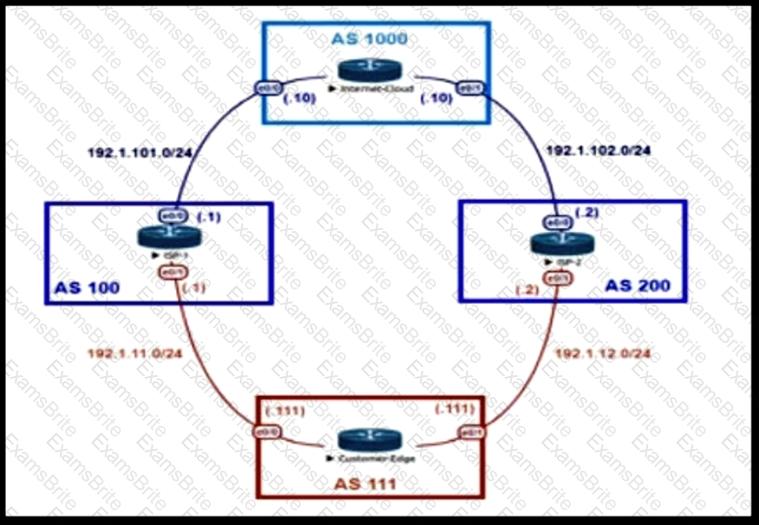
An engineer is designing the traffic flow for AS 111. Traffic from AS 111 should be preferred via AS 100 for all external routes. A method must be used that only affects AS 111. Which BGP attributes are best suited to control outbound traffic?
With virtualization applied throughout the network, every physical link may carry one or more virtual links. What is a key drawback of this?
What is a web-based model in which a third-party provider hosts applications that are available to customers over the Internet?
You are designing a large-scale DMVPN network with more than 500 spokes using EIGRP as the IGP protocol. Which design option eliminates potential tunnel down events on the spoke routers due to the holding time expiration?
Router R1 is a BGP speaker with one peering neighbor over link " A " . When link " A " fails, routing announcements are terminated, which results in the tearing down of the state for all BGP routes at each end of the link. What is this a good example of?
When constraint-based routing is under consideration to be added to a network design, what are two inherent characteristics or impacts that must be considered? (Choose two)
A customer migrates from a traditional Layer 2 data center network into a new SDN-based spine-and-leaf VXLAN EVPN data center within the same location. The networks are joined to enable host migration at Layer 2. What is the final migration step after hosts have physically migrated to have traffic flowing through the new network without changing any host configuration?
Which three tools are used for ongoing monitoring and maintenance of a voice and video environment? (Choose three.)
: 477
An organization is working on a design solution for a new Internet-based remote access virtual private network that has 1000 remote sites. A network administrator recommends GETVPN as the model What is a potential problem of using GETVPN in this situation?
Which solution component helps to achieve rapid migration to the cloud for SaaS and public cloud leveraging SD-WAN capabilities?
Company XYZ wants to redesign the Layer 2 part of their network and wants to use all available uplinks for increased performance They also want to have end host reachability supporting conversational learning However, due to design constraints, they cannot implement port-channel on the uplinks Which other technique can be used to make sure the uplinks are in active/active state?
Refer to the exhibit.
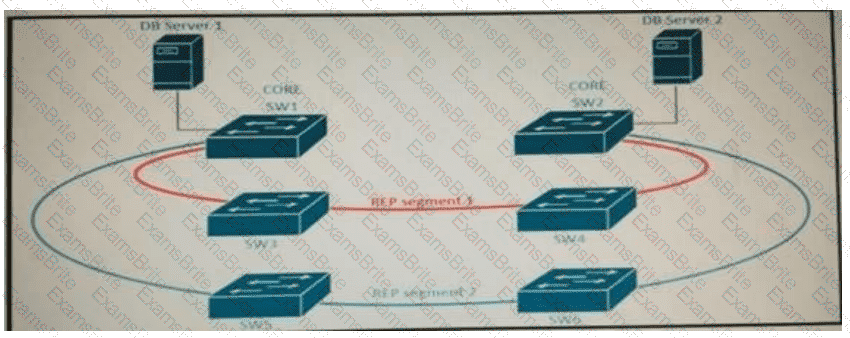
Refer to the exhibit. A new high availability DB server cluster is installed in the network. These two servers require high bandwidth and low latency Layer 2 connectivity for database replication.
Which solution supports these requirements?
Which hybrid cloud environment enables businesses to more readily stage data-intensive and time-sensitive tasks closer to the source, which reduces latency, eases networking requirements, and improves data protection?
A customer has a functional requirement that states HR systems within a data center should be segmented from other systems that reside in the same data center and same VLAN. The systems run legacy applications by using hard-coded IP addresses. Which segmentation method is suitable and scalable for the customer?
Which two protocols are used by SDN controllers to communicate with switches and routers? (Choose two.)
SDN emerged as a technology trend that attracted many industries to move from traditional networks to SDN. Which challenge is solved by SDN for cloud service providers?
Which main IoT migration aspect should be reviewed for a manufacturing plant?
In the wake of a security compromise incident where the internal networks were breached by an outside attacker at the perimeter of the infrastructure, an enterprise is now evaluating potential measures that can help protect against the same type of incident in the future. What are two design options that can be employed? (Choose two)
Company XYZ allows employees to use any open desk and plug their laptops in. They want authentication using domain credentials and future capability for segmentation within the same subnet. Which protocol can be recommended?
Which aspect of BGP-LS makes it scalable in large network when multiarea topology information must be gathered?
A business requirement stating that failure of WAN access for dual circuits into an MPLS provider for a Data Centre cannot happen due to related service credits that would need to be paid has led to diversely routed circuits to different points of presence on the provider’s network. What should a network designer also consider as part of the requirement?
Which two benefits can software-defined networks provide to businesses? (Choose two.)
You are designing a network running both IPv4 and IPv6 to deploy QoS. Which consideration is correct about the QoS for IPv4 and IPv6?
Which two compliance audit functions are useful to meet business requirements? (Choose two.)
Which function is performed at the access layer of the three-layer hierarchical network design model?
: 504
To facilitate true end-to-end QoS on an IP-network, the IETF has defined two models: IntServ and DiffServ Which protocol is used by both models?
A consultant needs to evaluate project management methodologies for a new service deployment on the existing network of a customer. The customer wants to be involved in the end-to-end project progress and be provided with frequent updates. The customer also wants the ability to change the requirements if needed, as the project progresses. Which project management methodology should be used?
An architect receives a business requirement from a CTO that states the RTO and RPO for a new system should be as close as possible to zero. Which replication method and data center technology should be used?
What are two parameters that can be leveraged by SAML in mixed private/public cloud environments by using identity and asset management? (Choose two)
Which architecture does not require an explicit multicast signaling protocol, such as PIM or P2MP, to signal the multicast state hop-by-hop, but instead uses a link state protocol to advertise the multicast forwarding state?
Which two advantages of using DWDM over traditional optical networks are true? (Choose two.)
Company XYZ plans to run OSPF on a DMVPN network. They want to use spoke-to-spoke tunnels in the design. What is a drawback or concern in this type of design?
During initial preparations to deploy 802 1x for wired access to their network, a company must ensure that the solution complies with existing internal security policies These policies mandate that every Auth C/Auth Z request must be protected by a tunnel which authenticates both server and clients using their PKI AI the same time, the user authentication phase must be independent of the tunnel Which scheme meets the requirements?
How can EIGRP topologies be designed to converge as fast as possible in the event of a point-to-point link failure?
The CIA triad is foundational to information security, and one can be certain that one or more of the principles within the CIA triad has been violated when data is leaked or a system is attacked Drag and drop the countermeasures on the left to the appropriate principle section on the right in any order
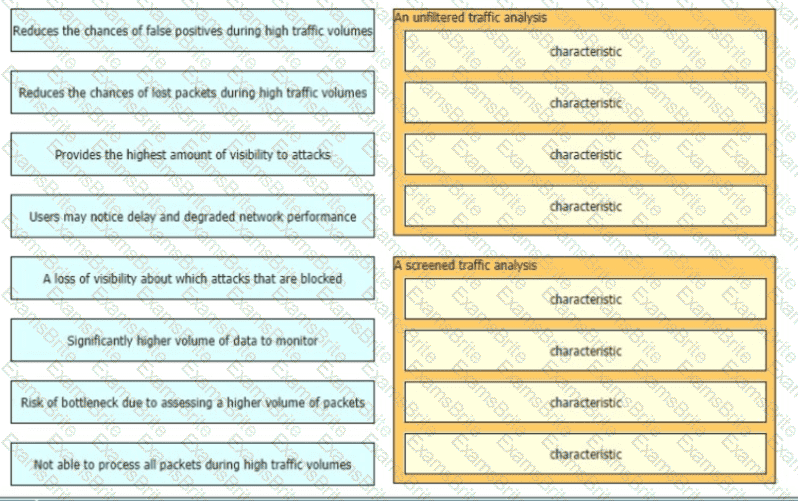
When a detection system for protecting a network from threats sourced from the Internet is designed there are two common deployment methods, where the system is placed differently relative to the perimeter firewall
•An unfiltered detection system examines the raw Internet data streams before it reaches the firewall
•A screened detection solution which monitors traffic that is allowed through the firewall Both have its advantages and disadvantages drag and drop the characteristics on the left to the corresponding category on the right in no particular order.
The controller has a global view of the network, and it can easily ensure that the network is in a consistent and optimal configuration. Which two statements describe a centralized SDN control path? (Choose two.)
A global e-commerce company is expanding its operations and planning to migrate its entire infrastructure to a hybrid cloud solution. They are concerned about data governance and want to ensure that their customers ' data is treated with utmost respect to sovereignty and privacy. What is an appropriate approach?
Which two types of planning approaches are used to develop business-driven network designs and to facilitate the design decisions? (Choose two)
Refer to the exhibit.
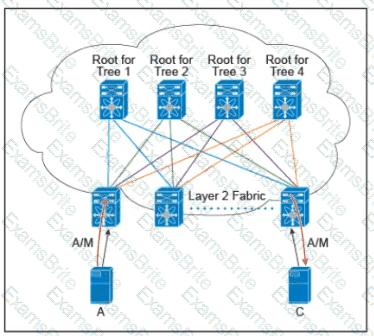
There are multiple trees in the Cisco FabricPath. All switches in the Layer 2 fabric share the same view of each tree. Which two concepts describe how the multicast traffic is load-balanced across this topology? (Choose two.)
Which action must be taken before new VoIP systems are implemented on a network to ensure that the network is ready to handle the traffic?
SDN is still maturing. Throughout the evolution of SDN, which two things will play a key role in enabling a successful deployment and avoiding performance visibility gaps in the infrastructure? (Choose two.)
Company XYZ, a global content provider, owns data centers on different continents. Their data center design involves a standard three-layer design with a Layer 3-only core. VRRP is used as the FHRP. They require VLAN extension across access switches in all data centers and plan to purchase a Layer 2 interconnection between two of their data centers in Europe. In the absence of other business or technical constraints, which termination point is optimal for the Layer 2 interconnection?
Refer to the exhibit.
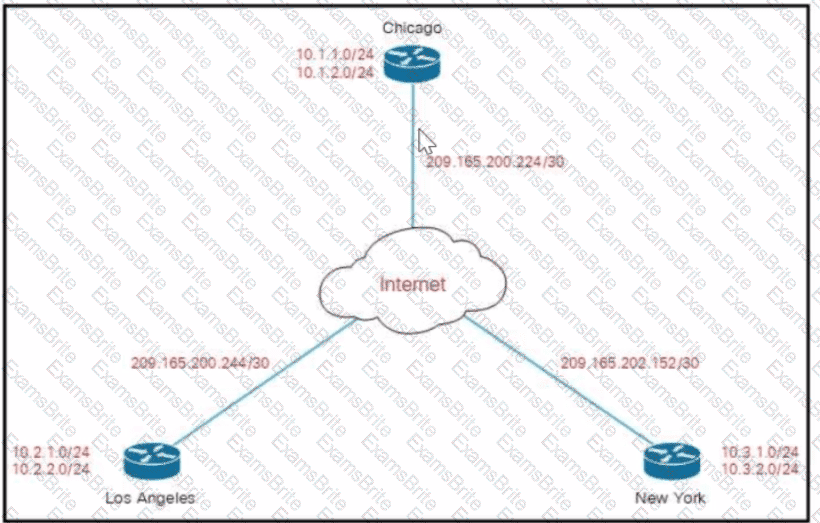
Company XYZ must design a DMVPN tunnel between the three sites. Chicago is going to act as the NHS, and the company wants DMVPN to detect peer endpoint failures. Which technology should be used in the design?
: 484
Traditionally networks handled static web pages e-mail and routine client/server traffic Today enterprise networks must handle more sophisticated types of network applications that include voice and video Applications place increasing demands on IT infrastructures as they evolve into highly visible services that represent the face of the business to internal and external audiences The large amount and variety of data requires that the modern network be aware of the content earned across it to optimally handle that content. Which service provide this intelligence?
Hybrid cloud computing allows organizations to take advantage of public and private cloud models. Which best practice should organizations follow to ensure data security in the private cloud?
You are designing a new Ethernet-based metro-area network for an enterprise customer to connect 50 sites within the same city. OSPF will be the routing protocol used. The customer is primarily concerned with IPv4 address conservation and convergence time. Which two combined actions do you recommend? (Choose two)
: 491
Budget is one of the important factors when you design a network Regardless of who controls the budget, one common network design goal is to contain costs Reduced budgets or limited resources often force network designers to select the most affordable solution instead of the best solution Which two elements must be considered when you do ROI analysis for the network design that explains how quickly the new network w ill pay for itself’ (Choose two. )
Refer to the exhibit.
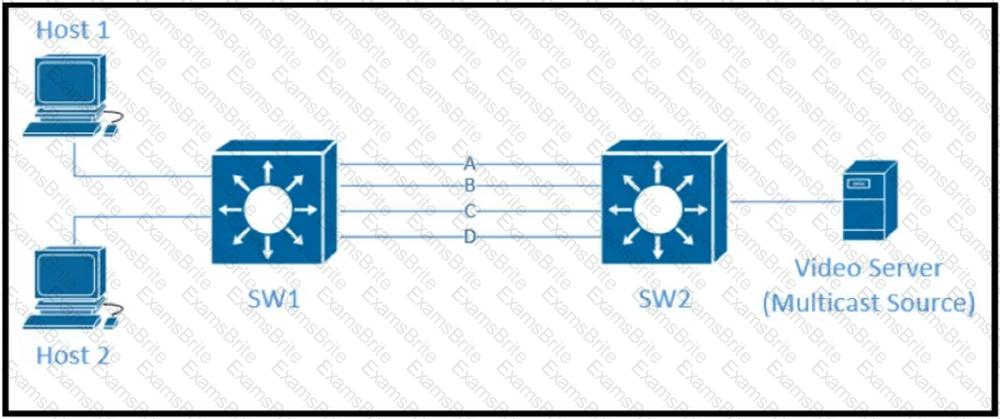
Traffic was equally balanced between Layer 3 links on core switches SW1 and SW2 before an introduction of the new video server in the network. This video server uses multicast to send video streams to hosts and now one of the links between core switches is overutilized. Which design solution solves this issue?
Company XYZ asks for design recommendations for Layer 2 redundancy. The company wants to prioritize fast convergence and resiliency elements. In the design, which two technologies are recommended? (Choose two.)
Most security monitoring systems use a signature-based approach to detect threats. In which two instances are systems based on Network Behavior Anomaly Detection better than signature-based systems when it comes to detecting security threat vectors? (Choose two.)
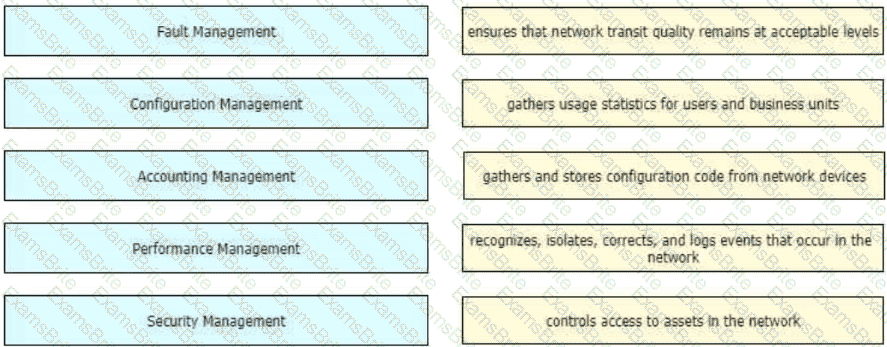
Drag and drop the FCAPS network management reference models from the left onto the correct definitions on the right.
A lead network architect is tasked with designing the optimal cloud-based solution for a rapidty growing e-commerce company that heavily relies on its online platform for sales and customer interactions The company’s business critical operations induce real time inventory management, order processing, and payment processing The executive team has decided to migrate their infrastructure to the cloud to improve scalability and recoce operational costs Which cloud service model(s) needs to considered?
Company XYZ has 30 sites running a legacy private WAN architecture that connects to the Internet via multiple high-speed connections. The company is now redesigning their network and must comply with these design requirements:
Use a private WAN strategy that allows the sites to connect to each other directly and caters for future expansion.
Use the Internet as the underlay for the private WAN.
Securely transfer the corporate data over the private WAN.
Which two technologies should be incorporated into the design of this network? (Choose two.)
A software-defined network exposes an API to the RIB and forwarding engine, allowing off-box control of routing—what SDN model is used?
Which DCI technology utilizes a “flood and learn” technique to populate the Layer 2 forwarding table?
When an SDN-based model is used to transmit multimedia traffic, which aspect should an architect consider while designing the network?
An IT service provider is upgrading network infrastructure to comply with PCI security standards. The network team finds that 802.1X and VPN authentication based on locally-significant certificates are not available on some legacy phones. Which workaround solution meets the requirement?
The Agile Manifesto is a document that defines the key values and principles behind the Agile philosophy and helps development teams work more efficiently and sustainably. Each of the four key values is split into two sections—a left-hand side and a right-hand side. In other words, though there is value in the items on the right, we value the items on the left more. What is one of the key values of the Agile Manifesto?
Company XYZ is designing the network for IPv6 security and they have these design requirements:
A switch or router must deny access to traffic from sources with addresses that are correct but topologically incorrect.
Devices must block Neighbor Discovery Protocol resolution for destination addresses not found in the binding table.
Which two IPv4 security features are recommended for this company? (Choose two)
Refer to the exhibit.
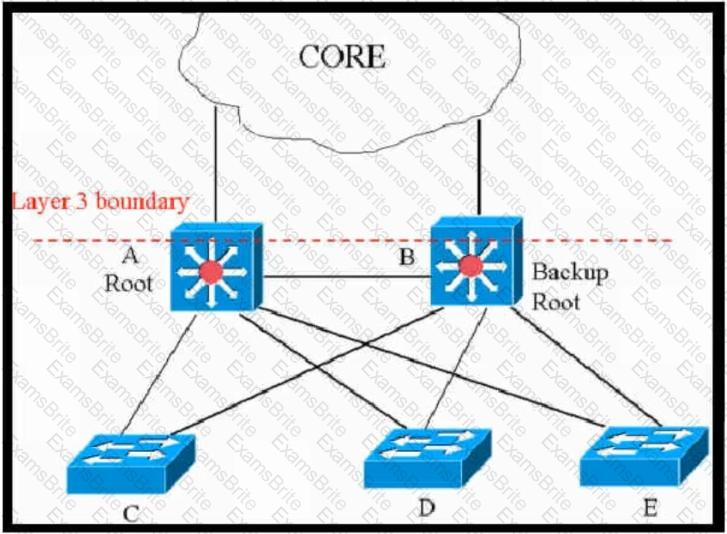
This network is running legacy STP 802.1d. Assuming " hello_timer " is fixed to 2 seconds, which parameters can be modified to speed up convergence times after single link/node failure?
Company XYZ needs advice in redesigning their legacy Layer 2 infrastructure. Which technology should be included in the design to minimize or avoid convergence delays due to STP or FHRP and provide a loop-free topology?
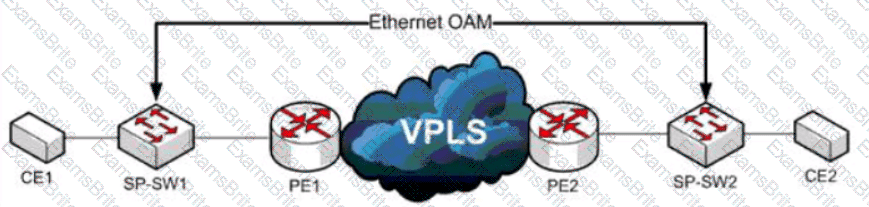
Refer to the exhibit. A service provider has a requirement to use Ethernet OAM to detect end-to-end connectivity failures between SP-SW1 and SP-SW2. Which two ways to design this solution are true? (Choose two)
Refer to the exhibit.
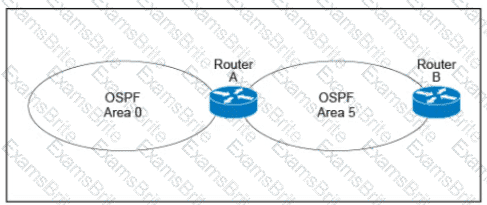
A customer runs OSPF with Area 5 between its aggregation router and an internal router. When a network change occurs in the backbone, Area 5 starts having connectivity issues due to the SPF algorithm recalculating an abnormal number of times in Area 5. You are tasked to redesign this network to increase resiliency on the customer network with the caveat that Router B does not support the stub area. How can you accomplish this task?
While designing a switched topology, in which two options is UplinkFast recommended? (Choose two.)
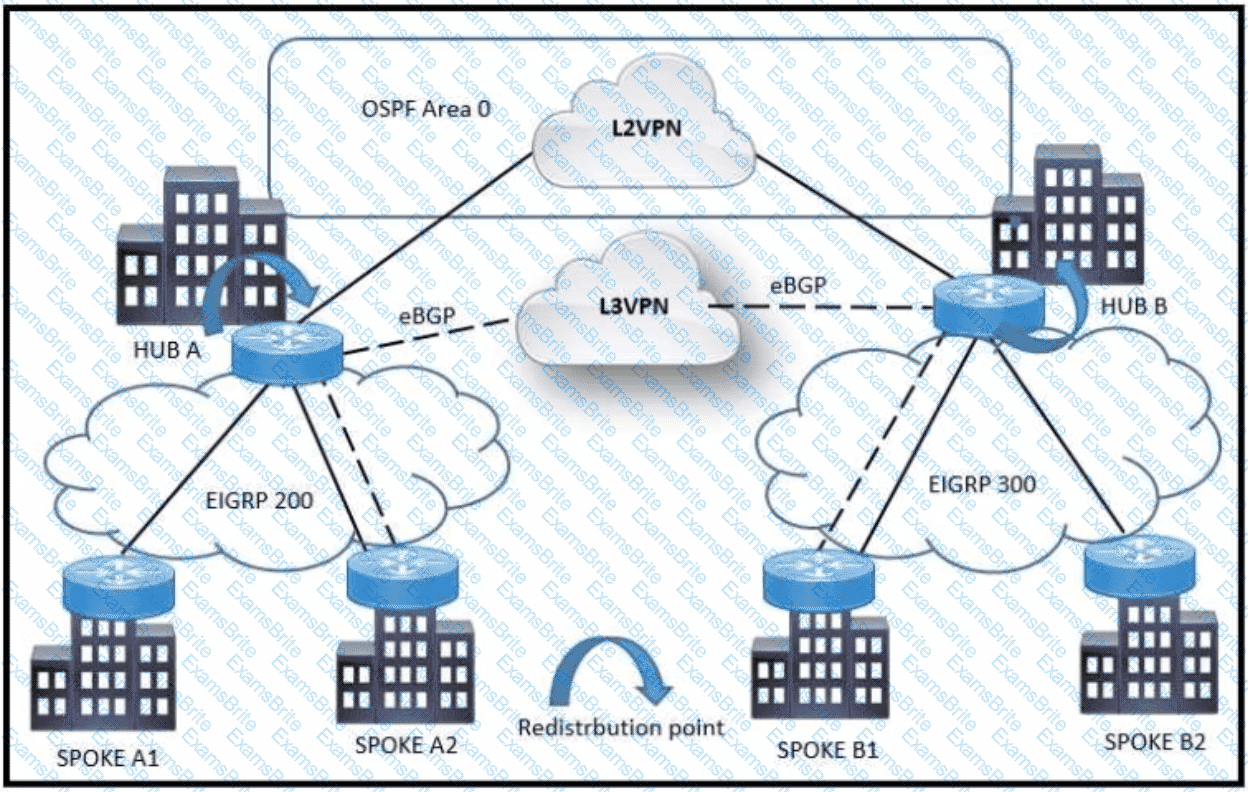
Refer to the exhibit: A customer is migrating from a TDM-based Layer 2 VPN (L2VPN) to an MPLS Layer 3 VPN (L3VPN) in phases. The backbone OSPF connection between HUB A and HUB B will be replaced by eBGP. During the migration, some spokes (A2 and B1) are already moved to the L3VPN. The goal is to avoid routing loops during this hybrid transition.
Which design choice helps prevent routing loops during the backbone link migration?
Company XYZ is designing their network using the three-layer hierarchical model. At which layer must the QoS design classify or mark the traffic?
: 486
An aerospace firm is considering implementing AI and ML systems to boost output while decreasing line downtime Optimal maintenance schedules and failure prediction of equipment are the end goals
To meet this business demand, which AI/ML solution would be the most effective in boosting productivity and decreasing downtime?
SDN controllers need to sustain healthy operation under the pressure of different objectives from the applications they host. High availability can be achieved through improved southbound APIs and controller placement heuristics and formal models. Which two implementation strategy help to maximize resilience and scalability? (Choose two.)
In a controller-based network architecture, between which of the two elements the southbound interface does the communication happen with a goal to program the data plane forwarding tables? (Choose two)
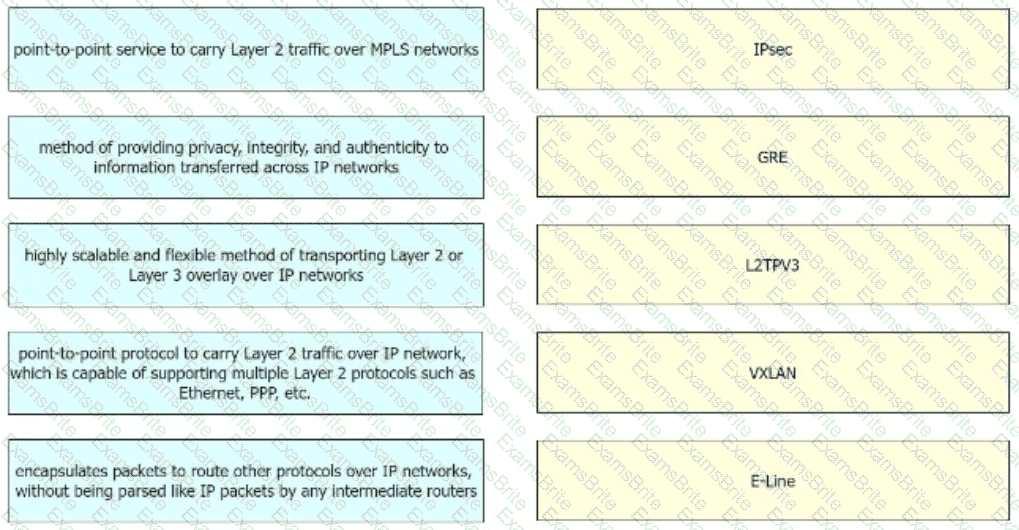
Drag and drop the right functional descriptions from the left onto the corresponding protocols on the right.
You are designing an Out of Band Cisco Network Admission Control Layer 3 Real-IP Gateway deployment for a customer. Which VLAN must be trunked back to the Clean Access Server from the access switch?
An existing wireless network was designed to support data traffic only. You must now install context-aware services for location tracking. What changes must be applied to the existing wireless network to increase the location accuracy? (Choose two)
Which three items do you recommend for control plane hardening of an infrastructure device? (Choose three.)
You are designing the QoS policy for a company that is running many TCP-based applications. The company is experiencing tail drops for these applications. The company wants to use a congestion avoidance technique for these applications. Which QoS strategy can be used?
Setting a specific goal for throughput based on per-second data rates between end hosts does not identify the requirements for specific applications When specifying throughput goals for applications, it is important to understand the throughput requirements for each application Which two factors that can constrain application layer throughput? (Choose two.)
The network designer needs to use GLOP IP addresses in order to make them unique within their ASN. Which multicast address range should be used?
Company XYZ is designing the IS-IS deployment strategy for their multiarea IS-IS domain. They want IS-IS neighbor relationships minimized on each segment and the LSDB size optimized. Which design can be used?
: 497 DRAG DROP
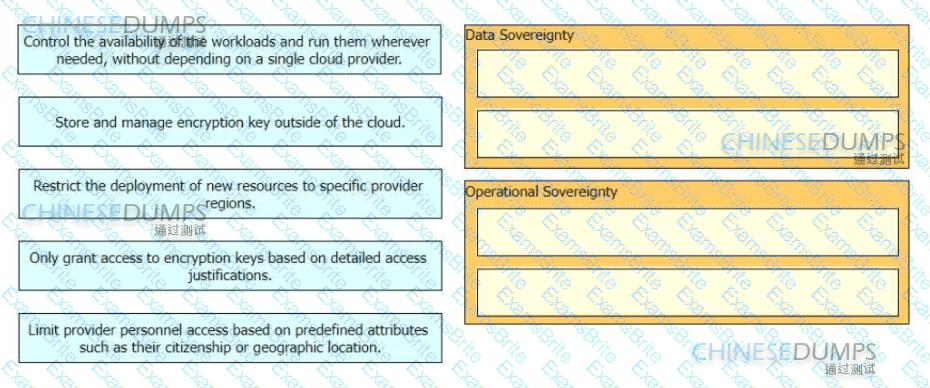
Data residency and sovereignty requirements are based on regional and industry-specific regulations, and different organizations have different data sovereignty requirements. Implementation of a mechanism that provides control over all access to data by cloud providers and the ability to inspect changes to cloud infrastructure and services is required. Drag and drop the descriptions from the left onto the corresponding categories on the right in no particular order. Not all options are used.
As more links are added to the network, information and attributes related to the link is added to the control plane, meaning every link that gets added will slow down the convergence of the control plane by some measurable amount of time As a result when additional redundancy is built or added the MTTR will increase too Which risk increases along with the increased MTTR?
A service provider hires you to design its new managed CE offering to meet these requirements:
The CEs cannot run a routing protocol with the PE.
Provide the ability for equal or unequal ingress load balancing in dual-homed CE scenarios.
Provide support for IPv6 customer routes.
Scale up to 250,000 CE devices per customer.
Provide low operational management to scale customer growth.
Utilize low-end (inexpensive) routing platforms for CE functionality.
Which tunneling technology do you recommend?
Company XYZ has implemented policy-based routing in their network. Which potential problem must be kept in mind about network reconvergence and PBR?
Which Interconnectivity method offers the fastest convergence in the event of a unidirectional issue between three Layer 3 switches connected together with routed links in the same rack in a data center?
Which technique facilitates analytics and knowledge discovery in big data systems to recognize hidden and complex patterns?
Modem IT departments are more service oriented than they used to be To meet the needs oí their customers. IT departments are spending more time analyzing and documenting their processes for delivering services A focus on processes helps to ensure effective service delivery and to avoid wasted expenditures on technology that doesn ' t provide a needed service What defines frameworks and processes that can help an organization match the delivery of IT services with the business needs of the organization?
How must the queue sizes be designed to ensure that an application functions correctly?
A customer with two 10 Mbps Internet links (active-active) experiences degraded performance when one fails. Static routing is used, and bandwidth upgrades aren ' t possible. The design must be failure-resistant without increasing CAPEX.
Which solution should be proposed?
A Service Provider is designing a solution for a managed CE service to a number of local customers using a single CE platform and wants to have logical separation on the CE platform using Virtual Routing and Forwarding (VRF) based on IP address ranges or packet length. Which is the most scalable solution to provide this type of VRF Selection process on the CE edge device?
Which three items do you recommend for control plane hardening of an infrastructure device? (Choose three.)
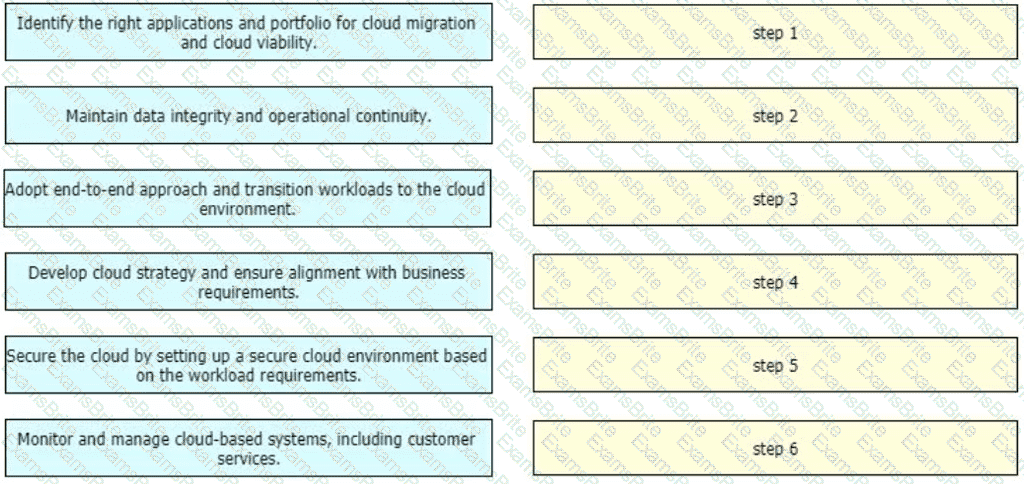
An enterprise wants to migrate an on-premises network to a cloud network, and the design team is finalizing the overall migration process. Drag and drop the options from the left into the correct order on the right.
Company XYZ branch offices connect to headquarters using two links, MPLS and Internet. The company wants to design traffic flow so voice traffic uses MPLS and all other traffic uses either link, avoiding process switching. Which technique can be used?
You are tasked with the design of a high available network. Which two features provide fail closed environments? (Choose two.)
Company XYZ is migrating their existing network to IPv6. Some access layer switches do not support IPv6, while core and distribution switches fully support unicast and multicast routing. The company wants to minimize cost of the migration. Which migration strategy should be used?
When consumers that leverage IaaS reach 100% resource capacity, what can be used to redirect the overflow of traffic to the public cloud so there is no disruption to service?
A legacy enterprise is using a Service Provider MPLS network to connect its head office and branches. They want to extend the existing IP CCTV network to a new branch without routing changes or IP address changes. What is the best approach?
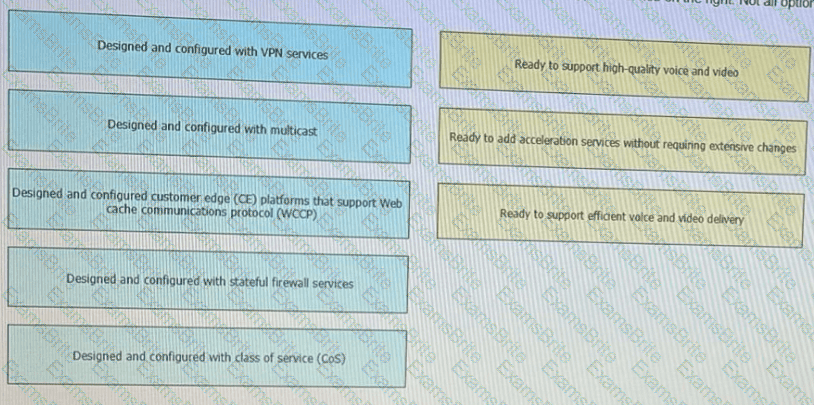
Flexibility, scalability, resiliency, and security are all chrematistics of a services-ready network An architecture featuring a modular design enables technologies and services to be added when the organization is ready to deploy. Drag and drop the design considerations on the left to the to type of service on the right Not all options are used
Company XYZ must design a strategy to protect their routers from DoS attacks, such as traffic destined to the router ' s own route processor, using separate control plane categories. Which two capabilities can be used to achieve this requirement? (Choose two.)
Two routers R1 and R2 are directly connected through an Ethernet link Both routers are running OSPF. OSPF has been registered with BFD and BFD is running in asynchronous mode with the echo function enabled Which two actions occur that are related to the echo function? (Choose two)
What are the two benefits of using northbound APIs in SDN architecture? (Choose two.)
Refer to the exhibit.
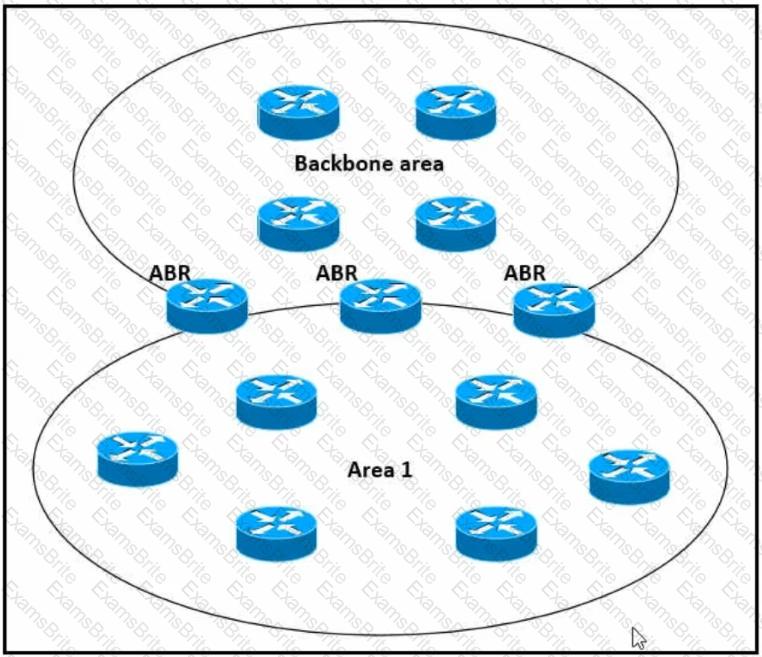
Which impact of using three or more ABRs between the backbone area and area 1 is true?
Which two statements describe the hierarchical LAN design model? (Choose two)
Which two features describe controller-based networking solutions compared to traditional networking solutions? (Choose two.)
Which protocol does an SD-Access wireless Access Point use for its fabric data plane?
There are varying requirements and motivations for improving the scalability and resilience of an enterprise application. The relative importance of these requirements and constraints varies depending on the type of app. the profile of the users, and the scale and maturity of the organization in which it is deployed. What are two common business drivers that deals with these aspects? (Choose two.)
The SD-WAN architecture is composed of separate orchestration, management, control, and data planes. Which activity happens at the orchestration plane?
Which methodology is the leading lifecycle approach to network design and implementation?
You have been asked to design a high-density wireless network for a university campus. Which two principles would you apply in order to maximize the wireless network capacity? (Choose two.)
Which two features are advantages of SD-WAN compared to MPLS-based connectivity? (Choose two.)
Which effect of using ingress filtering to prevent spoofed addresses on a network design is true?
Which SDN architecture component is used by the application layer to communicate with the control plane layer to provide instructions about the resources required by applications?
A senior network designer suggests that you should improve network convergence times by reducing BGP timers between your CE router and the PE router of the service provider. Which two factors should you consider to adjust the timer values? (Choose two.)
PaaS provides a cloud-based platform for developing, running, managing applications. Users access the PaaS through a GUI, where development or DevOps teams can collaborate on all their work across the entire application lifecycle including coding, integration, testing, delivery, deployment, and feedback. Which benefit does an organization get by using PaaS?
An external edge router provides connectivity from a service provider to an enterprise. Which two Internet edge best practices meet compliance regulations? (Choose two)
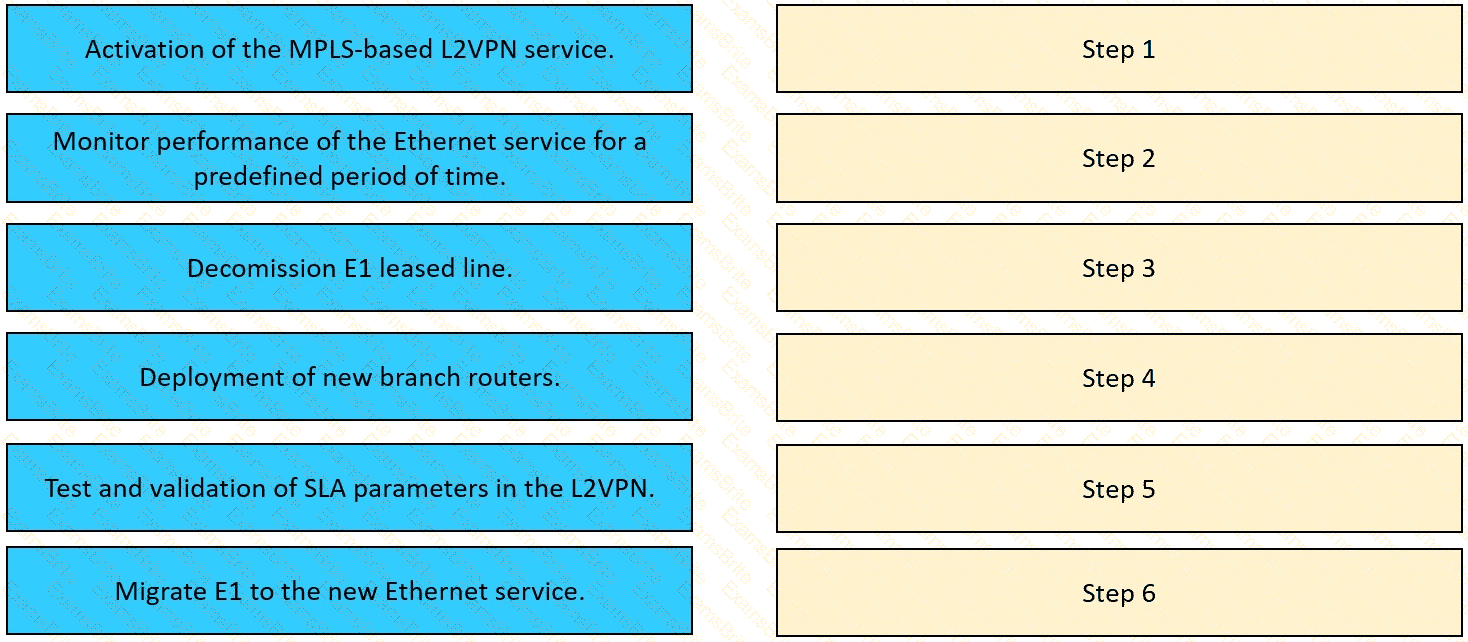
The network team in XYZ Corp wants to modernize their infrastructure and is evaluating an implementation and migration plan to allow integration MPLS-based, Layer 2 Ethernet services managed by a service provider to connect branches and remote offices. To decrease OpEx and improve
response times when network components fail, XYZ Corp decided to acquire and deploy new routers. The network currently is operated over E1 leased lines (2 Mbps) with a managed CE service provided by the telco.
Drag and drop the implementation steps from the left onto the corresponding targets on the right in the correct order.
Refer to the exhibit.
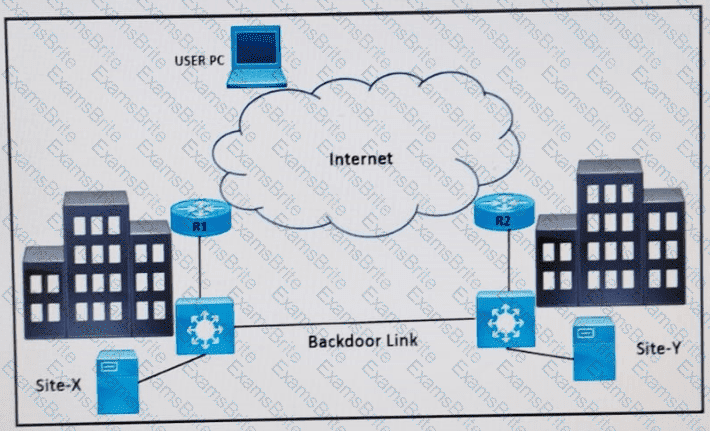
Refer to the exhibit. Two data center sites (X and Y) connect to the Internet and each other using a backdoor link. Both advertise the same IP prefix (100.75.10.0/23) to the Internet. Firewalls are behind R1 and R2.
Problem: When users attempt to reach 100.75.10.0/23, the return traffic is routed to Site-Y, regardless of where the session originated. This results in asymmetric traffic and potentially broken sessions due to firewall behavior.
Which design resolves the issue?
A key to maintaining a highly available network is building in the appropriate redundancy to protect against failure. This redundancy is carefully balanced with the inherent complexity of redundant systems. Which design consideration is relevant for enterprise WAN use cases when it comes to resiliency?
Which design method is achieved by layering the network control plane above a redundant physical infrastructure?
IPFIX data collection via standalone IPFIX probes is an alternative to flow collection from routers and switches. Which use case is suitable for using IPFIX probes?
A centralized control plane generally means one or more controllers gather the reachability and topology information from each switching device and calculate some part of the forwarding information at some place. How can a centralized control plane be defined or described?
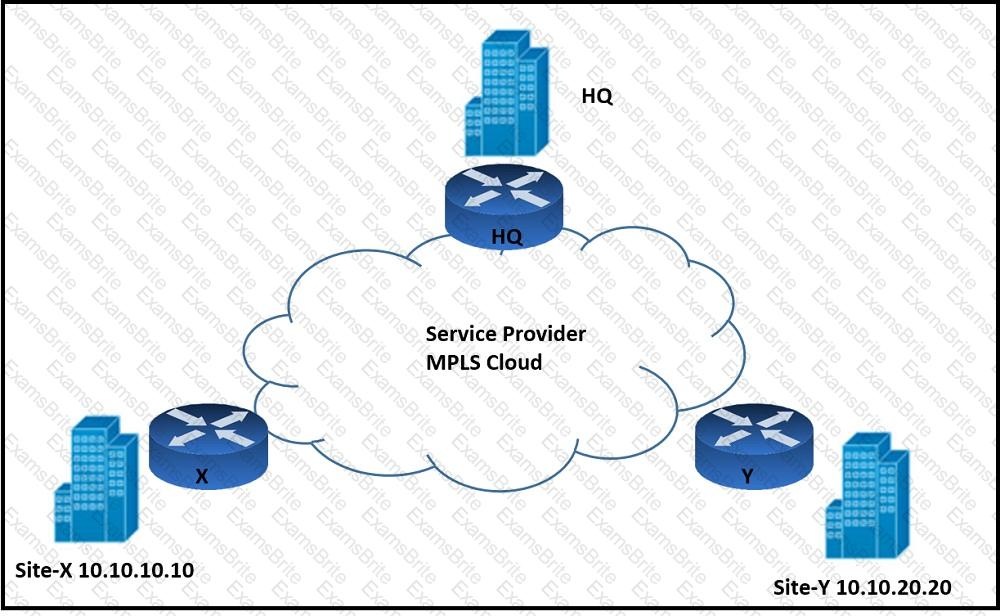
Refer to the exhibit. An architect must design an enterprise WAN that connects the headquarters with 22 branch offices. The number of remote sites is expected to triple in the next three years. The final solution must comply with these requirements:
Only the loopback address of each of the enterprise CE X and Y routers must be advertised to the interconnecting service provider cloud network.
The transport layer must carry the VPNv4 label and VPN payload over the MP-BGP control plane.
The transport layer must not be under service provider control.
Which enterprise WAN transport virtualization technique meets the requirements?
An enterprise plans to evolve from a traditional WAN network to a software-defined WAN network. The existing devices have limited capability when it comes to virtualization. As the migration is carried out, enterprise applications and services must not experience any traffic impact. Which implementation plan can be used to accommodate this during the migration phase?
A financial company requires that a custom TCP-based stock-trading application be prioritized over all other traffic for the business due to the associated revenue. The company also requires that VoIP be prioritized for manual trades. Which directive should be followed when a QoS strategy is developed for the business?
In outsourced IT services, the RTO is defined within the SLA. Which two support terms are often included in the SLA by IT and other service providers? (Choose two.)
Which two actions ensure voice quality in a branch location with a low-speed, high-latency WAN connection? (Choose two.)
Refer to the exhibit.
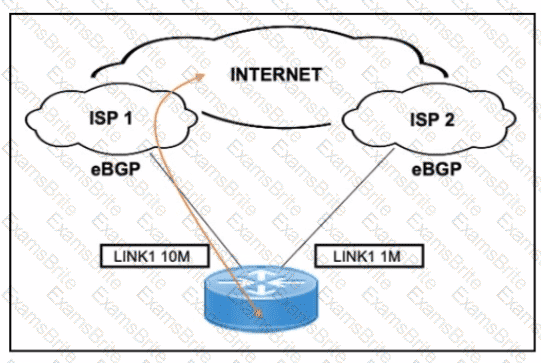
A customer has two eBGP internet links: one primary high-speed (10 Mbps) and one backup low-speed (1 Mbps). The requirement is to use the 10M link (ISP 1) for all inbound/outbound traffic and only use the 1M link (ISP 2) during failure.
What is the correct BGP-based design solution?
You have been tasked with designing a data center interconnect as part of business continuity. You want to use FCoE over this DCI to support synchronous replication. Which two technologies allow for FCoE via lossless Ethernet or data center bridging? (Choose two.)
Which two design options are available to dynamically discover the RP in an IPv6 multicast network? (Choose two)
Which option is a fate-sharing characteristic in regards to network design?
What advantage of placing the IS-IS Layer 2 flooding domain boundary at the core layer in a three-layer hierarchical network is true?