
Designing Cisco Security Infrastructure (300-745 SDSI) v1.0
Last Update May 31, 2026
Total Questions : 58
We are offering FREE 300-745 Cisco exam questions. All you do is to just go and sign up. Give your details, prepare 300-745 free exam questions and then go for complete pool of Designing Cisco Security Infrastructure (300-745 SDSI) v1.0 test questions that will help you more.



An oil and gas company recently faced a security breach when an employee’s notepad, which contained critical login credentials, was stolen. The incident led to unauthorized access to a user account, which posed a significant risk to sensitive company data and operations. The company wants to adopt a security measure that enhances user account protection. Which action must be taken to prevent breaches like this from happening in the future?
A global hotel chain is using Cisco ISE and Cisco switches to manage the network. The hotel company wants to enhance network security by segmenting users and endpoints. The company must ensure that devices within the same VLAN cannot communicate with each other. The goal is to prevent cross-communication without the use of dynamic access control lists. Which action must be taken using Cisco ISE to meet the requirement?
A manufacturing company experienced a security breach that resulted in sales data being compromised. An engineer participating in the investigation must identify who logged into the sales system during the affected period. Which approach must be used to gather the information?
After a recent security breach, a financial company is reassessing their overall security posture and strategy to better protect sensitive data and resources. The company already deployed on-premises next-generation firewalls at the network edge for each branch location. Security measures must be enhanced at the endpoint level. The goal is to implement a solution that provides additional traffic filtering directly on endpoint devices, thereby offering another layer of defense against potential threats. Which technology must be implemented to meet the requirement?
A retail company is facing a series of cyberattacks targeting web servers, which results in disruptions to online services. Upon investigation, the security team identified that these attacks involved invalid HTTP request headers, which were used to exploit vulnerabilities in the web application. To safeguard the company websites against similar threats in the future, the security team must deploy a security solution specifically designed to detect and block such malicious web traffic. Which security product must be used to protect the websites from similar attacks?
Refer to the exhibit.
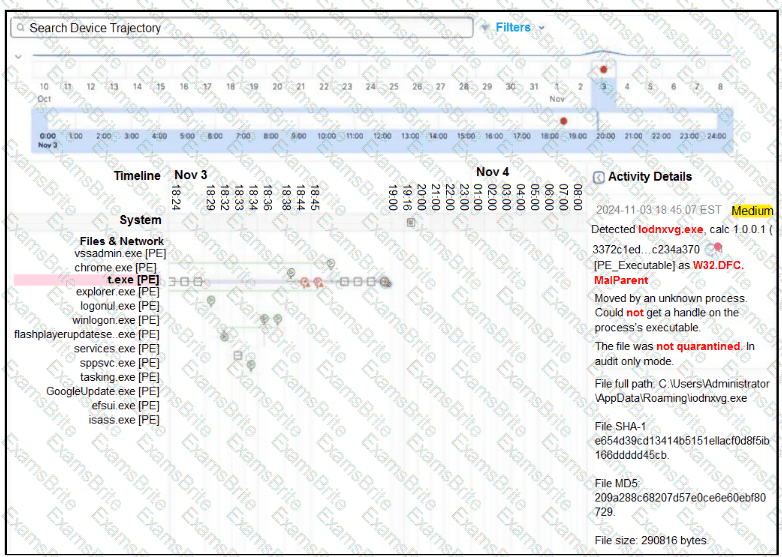
A retail company recently deployed a file inspection feature using secure endpoint. The file inspection must detect and prevent the execution of malicious files on machines. During testing, logs showed that certain malicious files are still being executed despite the presence of the security measure. To understand why the threats are not being blocked, it is essential to investigate the configuration of secure endpoint policies. Which configuration is allowing the files to execute?
A global energy company moved a monolithic application from the data center to public cloud. Over time, the company added many capabilities to the application, and it is now difficult for the application team to scale it. The application owner decided to modernize the application by moving to a Kubernetes cluster. However, he wants to ensure that the new application architecture provides a container network interface that is scalable, offers options for cloud-native security, and helps with visibility and observability. Which solution must be used to accomplish the task?
An IT company operates an application in a SaaS model. The administrative tasks, such as customer onboarding, within the application must be restricted to users who are on the corporate network where admins can access those functions via a web browser or a smartphone application. Which application technology must be used to provide granular control based on function?
Refer to the exhibit.
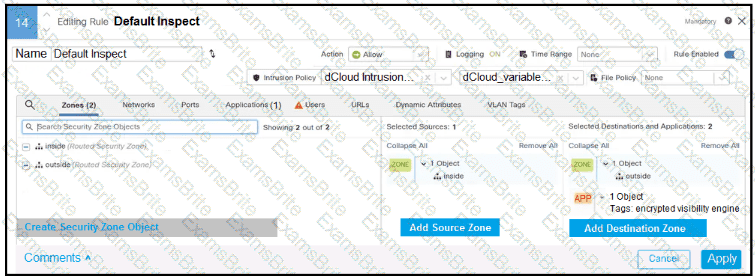
In addition to SSL decryption, which firewall feature allows malware to be blocked?
A manufacturing company recently experienced a network-down scenario due to malware spread on the management network. The company wants to implement a solution to detect and mitigate a similar threat in the future and protect the overall network. Which solution meets the requirements?
Which financial reporting regulatory framework must a publicly traded company doing business in the US comply with?
A software development company uses multiple cloud providers to host applications. The company is designing a scalable firewall solution that must meet the requirements:
Consistent security policies across multiple cloud environments.
Centralized visibility and management.
Scalability to accommodate different cloud platforms.
Which type of firewall meets the requirements?
A furniture company recently discovered that the endpoint detection and response configuration flagged several malicious files on company-managed laptops. The company must enhance security to prevent known malicious files from being delivered to the network and endpoints. The new solution must enhance the company’s ability to inspect and filter incoming traffic effectively. Which security product must be used to accomplish this goal?
A financial company is in the process of upgrading network access across the entire company. The solution must ensure: least privilege access control access across different network segments and increased security for employees. Which solution approach must the company take?
A developer is building new API functions for a cloud-based application. Before writing the code, the developer wants to ensure that destructive actions, including deleting and updating data, are properly protected by access control identifying sensitive fields such as those that contain passwords or personally identifiable information. Which approach must be used to score the risks proactively?
A technology company has many remote workers who access corporate resources from various locations. The company must ensure that security policies are managed and enforced directly on endpoints, and endpoints are protected from threats regardless of location. Which firewall architecture meets the requirements?