
Conducting Threat Hunting and Defending using Cisco Technologies for Cybersecurity 300-220 CBRTHD
Last Update May 31, 2026
Total Questions : 60
We are offering FREE 300-220 Cisco exam questions. All you do is to just go and sign up. Give your details, prepare 300-220 free exam questions and then go for complete pool of Conducting Threat Hunting and Defending using Cisco Technologies for Cybersecurity 300-220 CBRTHD test questions that will help you more.



A security team wants to create a plan to protect companies from lateral movement attacks. The team already implemented detection alerts for pass-the-hash and pass-the-ticket techniques. Which two components must be monitored to hunt for lateral movement attacks on endpoints? (Choose two.)
A mature SOC notices that several incidents over the past year involved attackers abusing legitimate administrative tools rather than deploying custom malware. Leadership asks the threat hunting team to improve detection coverage in a way that increases attacker cost rather than relying on easily replaceable indicators. Which detection strategy best aligns with this objective?
A SOC analyst using Cisco security tools wants to differentiatethreat huntingfromtraditional detection engineering. Which activity BEST represents threat hunting rather than detection engineering?
While investigating multiple incidents, analysts notice that attackers consistently use SMB for lateral movement and avoid PowerShell execution. Why is this observation valuable for attribution?
Refer to the exhibit.
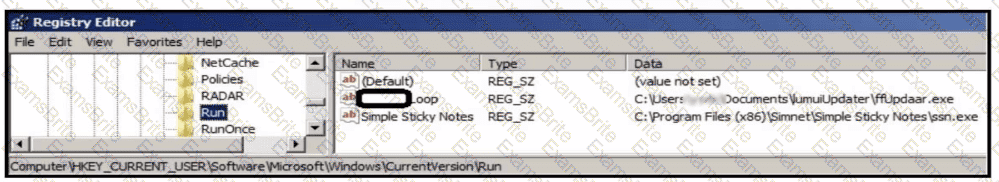
An analyst is evaluating artifacts and logs collected from recent breach. In the logs, ATP established persistency of malware by placing a path to the executable in a specific registry entry. What is the difference between the ATP's approach and using HKEY LOCAL MACHINE\Software\Microsoft\Windows\CurrentVersion\Run instead?
A security architect is designing a threat model for a multi-tier cloud application that includes public APIs, backend microservices, and an identity provider. The goal is to identify how an attacker could chain multiple weaknesses together to achieve account takeover and data exfiltration. Which threat modeling technique is MOST appropriate?
While analyzing telemetry from Cisco Secure Endpoint and Secure Network Analytics, analysts observe that an adversary consistently avoids deploying malware and instead abuses built-in administrative tools. Why does this observation matter for attribution?
During a structured hunt, analysts using Cisco SIEM tools complete hypothesis testing and confirm malicious activity. What is the NEXT step in the Cisco threat hunting lifecycle?
Which hunting technique is MOST effective for detecting stealthy data exfiltration over standard web protocols?
A security team is performing threat modeling for a hybrid environment consisting of on-prem Active Directory and Azure AD. The team wants to identify how an attacker could move from a compromised cloud identity to full on-prem domain dominance. Which modeling focus is MOST appropriate?
According to the MITRE ATT&CK framework, how is the password spraying technique classified?
The SOC team receives an alert about a user sign-in from an unusual country. After investigating the SIEM logs, the team confirms the user never signed in from that country. The incident is reported to the IT administrator who resets the user's password. Which threat hunting phase was initially used?
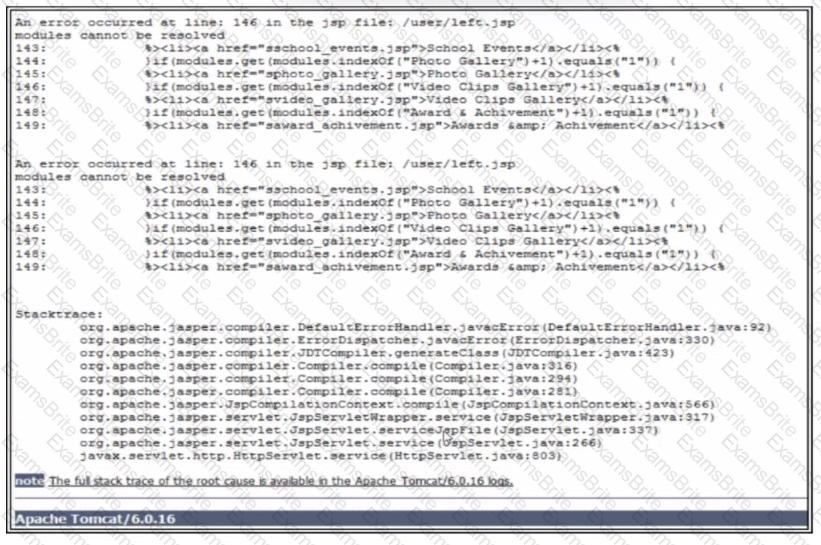
Refer to the exhibit. A penetration test performed against a web application generates the error message. Which two pieces of information are exposed? (Choose two.) Q Internal paths of the web server
The security team detects an alert regarding a potentially malicious file namedFinancial_Data_526280622.pdfdownloaded by a user. Upon reviewing SIEM logs and Cisco Secure Endpoint, the team confirms that the file was obtained from an untrusted website. The hash analysis of the file returns an unknown status. Which action must be done next?
A threat hunter is asked to model how an attacker could abuse cloud identity misconfigurations to escalate privileges without exploiting software vulnerabilities. Which modeling approach BEST supports this analysis?
A threat hunter wants to detect credential dumping attempts that bypass traditional malware detection. Which telemetry source is MOST effective for this purpose?