Threat Protection Administrator Exam
Last Update Apr 30, 2026
Total Questions : 72
We are offering FREE TPAD01 Proofpoint exam questions. All you do is to just go and sign up. Give your details, prepare TPAD01 free exam questions and then go for complete pool of Threat Protection Administrator Exam test questions that will help you more.



In the mail route configuration shown, how does the Protection Server attempt delivery to example.com?
Which of the following are true regarding Bounce Management?
Pick the 3 correct responses below.
Which application do you use to update the SSO configuration for Federated Authentication for your Proofpoint Cloud Services, including TAP, Cloud Admin, and NPRE?
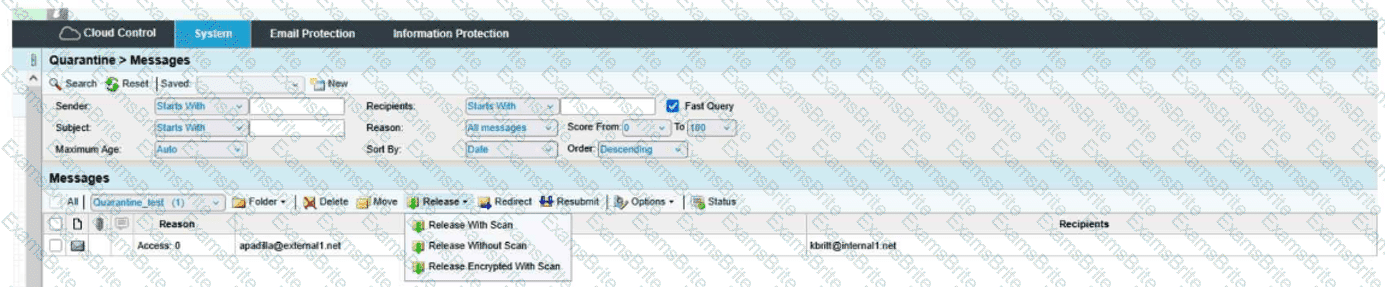
Based on the message details shown, which two actions are available to the administrator for this message?
An inbound message matches the inbound_protected policy route and also the default spam policy. Which policy will be applied?
Refer to the exhibit to see the interface used in this scenario.
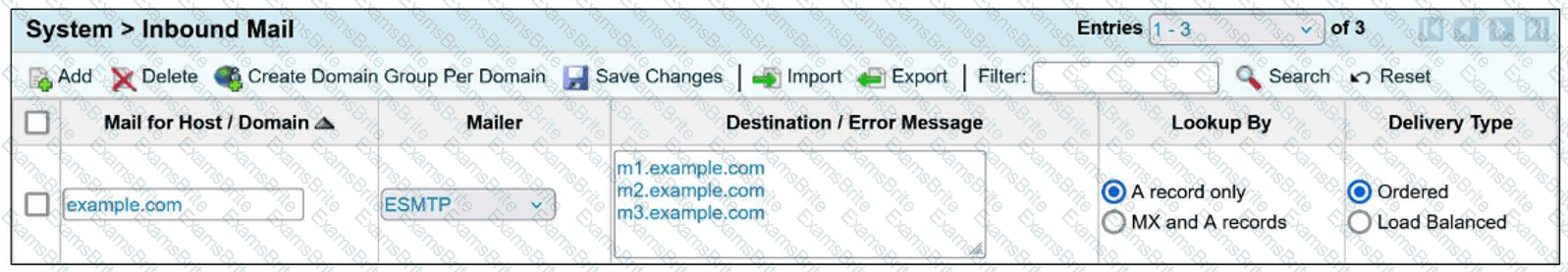
Which of the following is true regarding the inbound mail route?
As an administrator, you need to research why an email was sent instead of being blocked; where would you go in Cloud Admin to find which rule triggered the final disposition?
When employees at your company change their name, their email address also changes. To ensure that the user import process associates the new email addresses with the existing users, how should you configure the primary key?
You are reviewing the MTA logs for a message that has been deferred. Which Delivery Status Notification (DSN) code indicates that the receiving server was temporarily unable to process the message?
Can a new email digest be generated for every email which enters quarantine?
You have just been licensed to export the Smart Search data from your PoD protection server in JSON format. Where would you create the API keys needed by your SIEM to ingest the JSON stream?
When you are attempting to release a message from the quarantine folder, you have the three choices shown here. The option of Release Encrypted With Scan will do which of the following?
If one of your corporate email accounts is sending excessive outbound emails, the Outbound Throttle feature can help. Which of the following is true regarding Outbound Throttle?
Select from the following options, which are configurable in quarantine folder settings.
Pick the 3 correct responses below.
You can drag the divider between the question and exhibit to the left to make the image larger.
Refer to the exhibit.
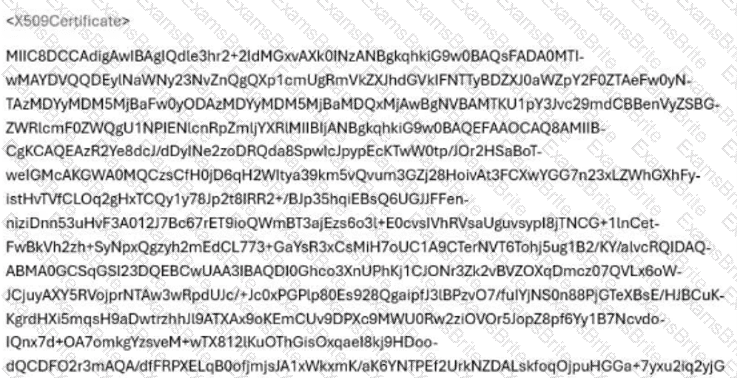
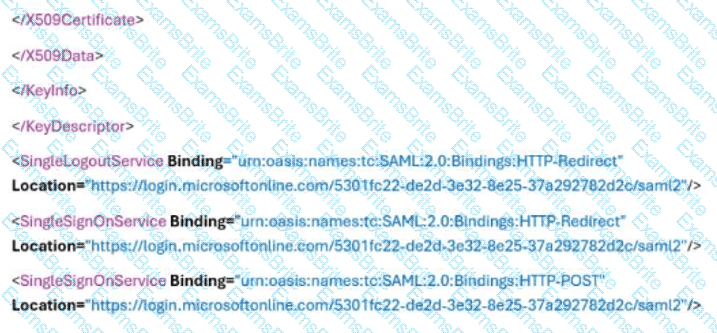
You are configuring SSO for Proofpoint Cloud Services, such as Cloud Admin, TAP Dashboard, Cloud Threat Response, CASB, and Identity Threat Response. The Microsoft O365 administrator sends you a portion of the XML file containing the SAML configuration. Which of the following strings should be entered in the “SAML Login Endpoint (required)” field in the Proofpoint Identity Provider Configuration?