
HCIA-Security V4.0 Exam
Last Update May 31, 2026
Total Questions : 153
We are offering FREE H12-711_V4.0 Huawei exam questions. All you do is to just go and sign up. Give your details, prepare H12-711_V4.0 free exam questions and then go for complete pool of HCIA-Security V4.0 Exam test questions that will help you more.



In most cases, a user applies for a local certificate from a CA, and the CA approves the application and issues the certificate to the user.
Which of the following statements is incorrect about information transmission through the heartbeat link between two firewalls that work in hot standby mode?
For which of the following parameters can the packet filtering firewall filter?
When logging in to the web UI through HTTPS, you need to specify a local certificate issued by a CA that the web browser trusts for the HTTPS client on the device. Because the web browser can verify the local certificate, this approach avoids malicious attacks and ensures secure logins of administrators.
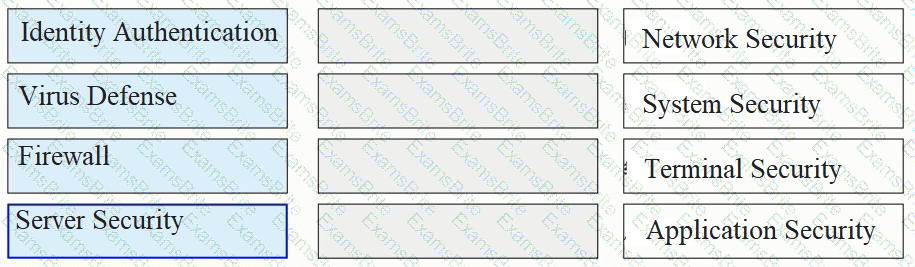
Please classify the following security defenses into the correct classification.
_____ Authentication is to configure user information (including local user's user name, password and various attributes) on the network access server. The advantage is that it is fast.[fill in the blank]*
Which of the following characteristics does a denial-of-service attack include?
The trigger authentication method for firewall access user authentication does not include which of the following?
On a firewall, security policies with the permit action do not need to be configured for traffic between users in the same zone.
At what layer does packet filtering technology in the firewall filter packets?
The trigger modes of the built-in Portal authentication in the firewall include pre-authentication and ____ authentication[fill in the blank]*
In the automatic backup mode of hot standby on the second machine, which of the following sessions is backed up?
Database operation records can be used as ___ evidence to backtrack security events.[fill in the blank]*
3-tuple NAT allows external devices to proactively access internal PCs through translated addresses and ports. Even if no security policy is configured on the firewall, the firewall allows such access packets to pass through.
Which of the following statements are correct about the PKI system structure?
Digital envelope technology means that the sender uses the receiver's public key to encrypt the data, and then sends the ciphertext to the receiver
When logging in to the web UI through HTTPS, you need to specify a local certificate issued by a CA that the web browser trusts for the HTTPS client on the device. Because the web browser can verify the local certificate, this approach avoids malicious attacks and ensures secure logins of administrators.
In the TCP/P protocol core, which of the following protocols works at the application layer?
Please match the following information security risks to information security incidents one by one.[fill in the blank]*
physical security risk Enterprise server permissions are loosely set
Information Security Management Risk Infected Panda Burning Incense
Information Access Risk Fire destroyed equipment in computer room
application risk Talk to people about leaking company secrets
DES is a stream encryption algorithm, because the cipher capacity is only 56 bits, so it is not enough to deal with the weakness of insufficient security, and later 3DES was proposed.
The following description of the construction of a digital certificate, which item is wrong
Which of the following is not the matching mode of the firewall security protection whitelist rules?
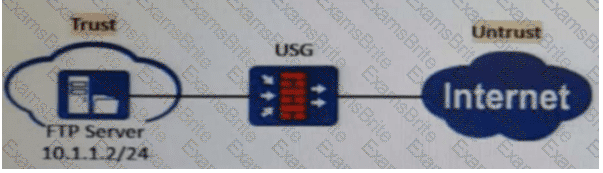
As shown in the figure, nat server global202.106.1.1 inside10.10.1.1 is configured on the firewall. Which of the following is the correct configuration for interzone rules?
Which type of NAT translates both addresses and port numbers and uses the public IP address of the outbound interface as the post-NAT address?
Both digital envelopes and digital signatures guarantee data security and verify the origin of data.
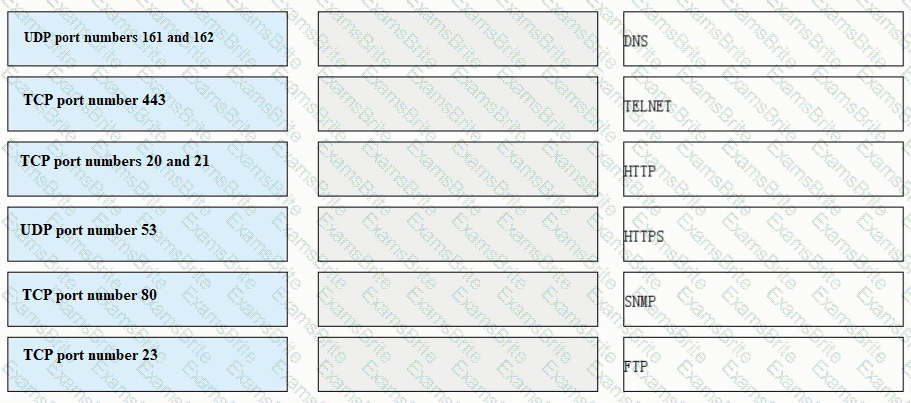
Match each of the following application layer service protocols with the correct transport layer protocols and port numbers.
Which of the following statements is correct about security zones on a Huawei firewall?
Which of the following statements are correct about IKE-based SA establishment in IPsec?
Which of the following descriptions about the heartbeat interface is wrong ( )?
In the Linux system, which of the following is the command to query the P address information?
In asymmetric encryption algorithms, only public keys can be used to encrypt data, and private keys are used to decrypt data. This process is irreversible.
Please order the following steps in the PKI life cycle correctly, 1. Issued, 2. storage, 3. Update, 4. verify[fill in the blank]*
IPSec VPN uses an asymmetric algorithm to calculate the ___ key to encrypt data packets.[fill in the blank]