Dell Security Foundations Achievement
Last Update Apr 21, 2026
Total Questions : 20
We are offering FREE D-SF-A-24 EMC exam questions. All you do is to just go and sign up. Give your details, prepare D-SF-A-24 free exam questions and then go for complete pool of Dell Security Foundations Achievement test questions that will help you more.



AR.T.I.E.'s business is forecast to grow tremendously in the next year, the organization will not only need to hire new employees but also requires contracting with third-party vendors to continue seamless operations.A .R.T.I.E.uses a VPN to support its employees on the corporate network, but the organization is facing a security challenge in supporting the third-party business vendors.
To better meetA .R.T.I.E.'s security needs, the cybersecurity team suggested adopting a Zero Trust architecture (ZTA). The main aim was to move defenses from static, network-based perimeters to focus on users, assets, and resources. Zero Trust continuously ensures that a user is authentic and the request for resources is also valid. ZTA also helps to secure the attack surface while supporting vendor access.
What is the main challenge that ZTA addresses?
AnA .R.T.I.E.employee received an email with an invoice that looks official for $200 for a one-year subscription. It clearly states: "Please do not reply to this email," but provides a Help and Contact button along with a phone number.
What is the type of risk if the employee clicks the Help and Contact button?
A Zero Trust security strategy is defined by which of the primary approaches?
The cybersecurity team must create a resilient security plan to address threats. To accomplish this, the threat intelligence team performed a thorough analysis of theA .R.T.I.E.threat landscape. The result was a list of vulnerabilities such as social engineering, zero-day exploits, ransomware, phishing emails, outsourced infrastructure, and insider threats.
Using the information in the case study and the scenario for this question, which vulnerability type exposes the data and infrastructure of A.R.T.I.E .?
A .R.T.I.E.is planning to deploy some of their applications in a public cloud. A major concern is how to share and protect data off premises. Also, how data can be used in decision making without exposing it to anyone who should not have access. Dell Services briefed them about various control mechanisms to secure data in the public cloud.
Which control mechanism should be selected in this scenario?
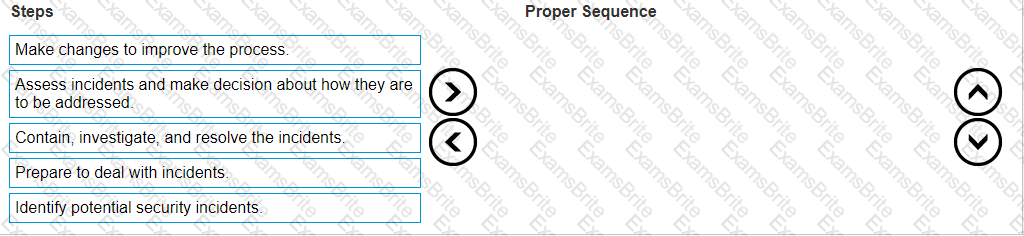
The cybersecurity team created a detailed security incident management procedures training program to manage any probable incidents atA .R.T.I.E.
Arrange the steps in the proper sequence to best manage cybersecurity incidents.