
CyberArk CDE-CPC Recertification
Last Update May 30, 2026
Total Questions : 99
We are offering FREE CPC-CDE-RECERT CyberArk exam questions. All you do is to just go and sign up. Give your details, prepare CPC-CDE-RECERT free exam questions and then go for complete pool of CyberArk CDE-CPC Recertification test questions that will help you more.



Which statements accurately describe the process of LDAP integration with CyberArk Privilege Cloud Standard? (Choose two.)
You want to add an additional maintenance user on the PSM for SSH. How can you accomplish this if InstallCyberArkSSHD is set to Integrated?
Which tool configures the user object that will be used during the installation of the PSM for SSH component?
Which option correctly describes the authentication differences between CyberArk Privilege Cloud and CyberArk PAM Self-Hosted?
Which components can be installed when running the Privilege Cloud Connector installation package? (Choose two.)
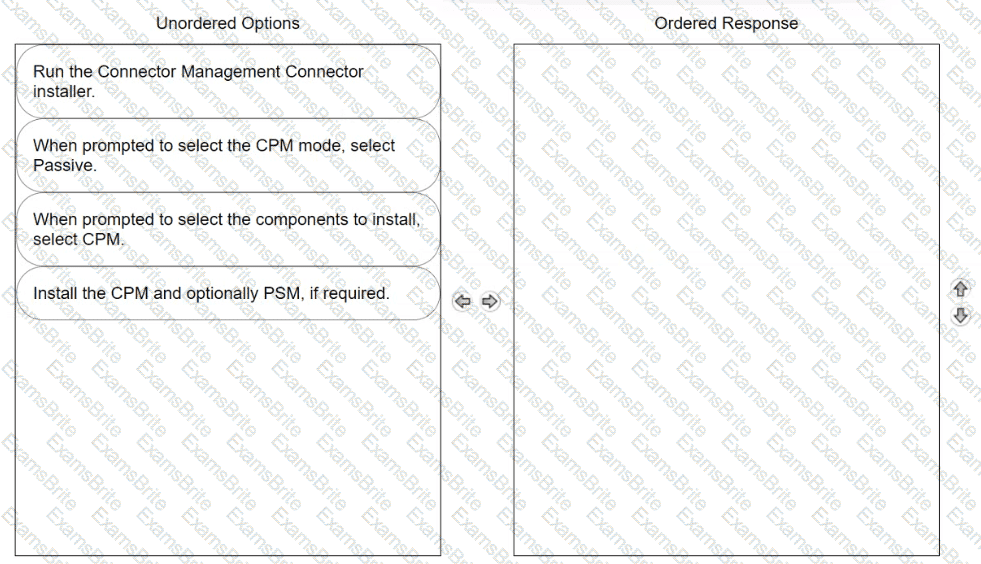
Arrange the steps to install passive CPM using Connector Management in the correct sequence
During CPM hardening, which locally created users are granted Logon as a Service rights in the local group policy? (Choose 2.)
You are planning to configure Multi-Factor Authentication (MFA) for your CyberArk Privilege Cloud Shared Service. What are the available authentication methods?
What must be specified when authenticating to Privilege Cloud during the Secure Tunnel install?
According to best practice, when considering the location of PSM Connector servers in Privilege Cloud environments, where should the PSM be placed?
Which ports do the CyberArk Identity Connector require to be opened to support using Active Directory for LDAP authentication to Privileged Cloud Shared Services? (Choose two.)
Which deployment criteria influences the CyberArk-provided hardening methods that need to be applied to CPM and PSM components?
(Typing correction / missing stem noted)
Your last item only lists answer choices (no question text). Based on Privilege Cloud documentation, these choices most commonly appear with the question:
“Which tools can be used to upgrade Privilege Cloud Connector components (CPM/PSM)?” (Choose two.)
What is determined by the MaxConcurrentConnections setting within a platform?
You are configuring an integration to provision users based on LDAP directory services for Privilege Cloud Shared Services. Which component must first be installed and configured in the environment to support this?
After the session has ended, where is the default final recording storage located?
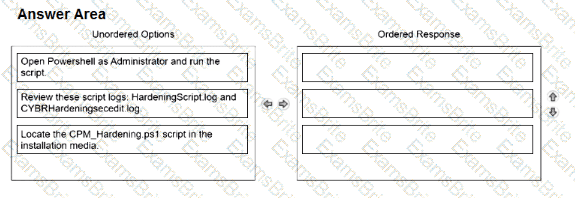
Arrange the steps to complete CPM Hardening for out-of-Domain deployment in the correct sequence.
You want to improve performance on the CPM by restricting accounts for the CYBRWINDAD platform to only the WINDEMEA and WINDEMEA_ADMIN Safes. How do you set this in CyberArk?
You plan to install Privilege Cloud Connectors on your AWS and Azure environments.
What is the maximum number of concurrent RDP/SSH sessions that each connector can handle for Large Implementations?
You have been tasked with deploying a Privilege Cloud PSM for SSH connector When the initial installation has successfully completed, you create and permission several maintenance users to be used for administering the connector.
Which configuration file must be updated to define these maintenance users?
A support team has asked you to provide the previous password for an account that had its password recently changed by the CPM. In which tab within the account's overview page can you retrieve this information?
Which file must you edit to ensure the PSM for SSH server is not hardened automatically after installation?
What must be done to configure the syslog server IP address(es) for SIEM integration? (Choose 2.)