
CC - Certified in Cybersecurity
Last Update May 30, 2026
Total Questions : 403
We are offering FREE CC ISC exam questions. All you do is to just go and sign up. Give your details, prepare CC free exam questions and then go for complete pool of CC - Certified in Cybersecurity test questions that will help you more.



Which one of the following controls is NOT particularly effective against the insider threat?
Embedded systems and network-enabled devices that communicate with the Internet are considered:
Removing the belief that a network has any trusted space and enforcing security at the most granular level is known as:
A centralized organizational function that monitors, detects, and analyzes security events to prevent disruptions is called:
John is concerned about a possible conflict of interest from a consulting side job. Which source should he consult?
Which technology should be implemented to increase the work effort required for buffer overflow attacks?
The process of applying secure configurations to reduce the attack surface is known as:
A transaction over $50,000 requires approval from both a manager and an accountant. Which concept applies?
Shaun is planning to protect data in all states (at rest, in motion, and in use), defending against data leakage. What is the BEST solution to implement?
A set of rules that everyone must comply with and that usually carry monetary penalties for noncompliance are:
Which TLS extension is used to optimize the TLS handshake process by reducing the number of round trips between the client and server?
Which uses encrypted, machine-generated codes to verify a user's identity?
Which type of network is set up similar to the internet but is private to an organization? Select the MOST appropriate answer.
A device that forwards traffic to the port of a known destination device is a:
What is the main purpose of using multi-factor authentication (MFA) in a security system?
A scam where a malicious website is made to look exactly like a trusted site is called:
Exhibit.
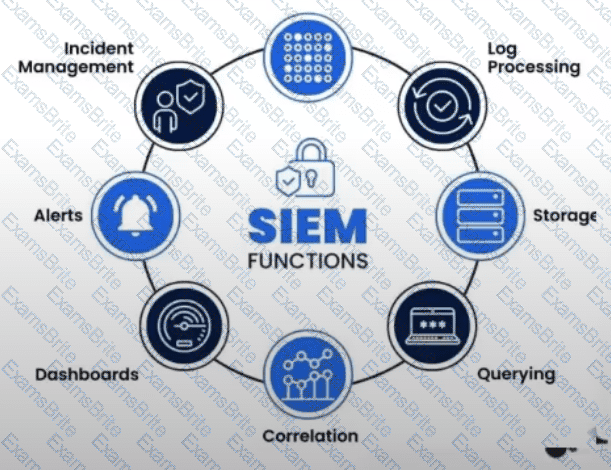
What is the purpose of a Security Information and Event Management (SIEM) system?
A security event in which an intruder gains or attempts unauthorized access to a system is called:
How many bits represent the Organizationally Unique Identifier (OUI) in MAC addresses?
A company wants employees to access resources from anywhere in the world. Which access control model is best?
Which attack most effectively maintains remote access and control over a victim’s computer?
An organization develops procedures to restore critical business processes after a major disruption. What plan is this?
A hacker launches a specific attack to exploit a known vulnerability. This is called:
What principle states that individuals should only have the minimum set of permissions necessary to carry out their job functions?
Which type of control is used to restore systems or processes to their normal state after an attack?
If a device is found to be non-compliant with the security baseline, what action should the security team take?
Which of the following vulnerabilities cannot be discovered during a routine vulnerability assessment?
Which type of risk involves unauthorized use or disclosure of confidential information such as passwords, financial data, or personal information?
A structured approach used to oversee and manage risk for an enterprise is called:
A measure of the degree to which an organization depends on information or systems to achieve its mission is called:
Governments can impose financial penalties as a consequence of breaking a:
Which aspect of cybersecurity is MOST impacted by Distributed Denial of Service (DDoS) attacks?
When operating in a cloud environment, which cloud deployment model provides security teams with the greatest access to forensic information?
The method of distributing network traffic equally across a pool of resources is called:
A weighted factor based on the probability that a threat will exploit a vulnerability is called:
A company wants to ensure that its employees can evacuate the building in case of an emergency. Which physical control is best suited?
Which cloud service model provides the most suitable environment for customers to build and operate their own software?
Which of the following is unlikely to be a member of the disaster recovery team?
A practitioner needing step-by-step instructions to complete a provisioning task should consult a:
Which principle states that users should have access only to the specific data and resources needed to perform required tasks?
Which is the most efficient and effective way to test a business continuity plan?
In which access control model can the creator of an object delegate permissions?
Which protocol would be most suitable to fulfill the secure communication requirements between clients and the server for a company deploying a new application?
Walmart has a large e-commerce presence worldwide. Which solution would ensure the LOWEST possible latency for customers using their services?
Which of the following is NOT one of the three main components of an SQL database?
Which one of the following cryptographic algorithms does NOT depend upon the prime factorization problem?
Which concept prevents crime by designing a physical environment that positively influences human behavior?
Mark is configuring an automated data transfer between two hosts and needs an authentication method. What approach is best suited?
Which of the following is often associated with Disaster Recovery planning?
When the ISC2 mail server sends mail to other mail servers, it becomes a —?
A company’s servers are down due to malware. What is the FIRST step the DR team should take?
The evaluation of security controls to determine whether they are implemented correctly and operating as intended is known as:
An ISC2 member is offered an illicit copy of a movie. What should they do?
A logical group of workstations, servers, and network devices that appear to be on the same LAN despite their geographical distribution.
Which provides confidentiality by hiding or obscuring a message so it cannot be understood by unauthorized parties?
Juli is listening to network traffic and capturing passwords as they are sent to the authentication server. She plans to use the passwords as part of a future attack. What type of attack is this?
Communication between end systems is encrypted using a key, often known as ________?
What is a security token used to authenticate a user to a web application, typically after they log in?
Which version of TLS is considered the most secure and recommended for use?
In which cloud model does the customer have theleast responsibilityover infrastructure?
A company experiences a major IT outage and cannot perform critical business functions. Which plan helps recovery?