
LPIC-1 Exam 102, Part 2 of 2, version 5.0
Last Update Apr 15, 2026
Total Questions : 235
We are offering FREE 102-500 LPI exam questions. All you do is to just go and sign up. Give your details, prepare 102-500 free exam questions and then go for complete pool of LPIC-1 Exam 102, Part 2 of 2, version 5.0 test questions that will help you more.



Which of the following commands can be used to convert text files in one character encoding to another character encoding?
Which command is used to add an empty group to the system? (Specify ONLY the command without any path or parameters.)
Which of the following commands should be added to /etc/bash_profile in order to change the language of messages for an internationalized program to Portuguese (pt)?
In which file, if present, must all users be listed that are allowed to use the cron scheduling system? (Specify the full name of the file, including path.)
Which of the following tasks can the date command accomplish? (Choose two.)
Why is /etc/shadow not world readable if the passwords are stored in an encrypted fashion?
What information related to a user account is modified using the change command?
Which of the following commands can identify the PID od a process which opened a TCP port?
How many IP addresses can be used for unique hosts inside the IPv4 subnet 192.168.2.128/26?
Which of the following statements about sytemd-journald are true? (Choose three.)
In an xinetd configuration file, which attribute specifies the network address that will be used to provide the service?
Which of the following programs uses the hosts.allow file to perform its main task of checking for access control restrictions to system services?
How can the existing environment variable FOOBAR be suppressed for the execution of the script./myscript only?
Which of the following files, when existing, affect the behavior of the Bash shell? (Choose TWO correct answers.)
What output will the following command sequence produce?
echo '1 2 3 4 5 6' | while read a b c; do
echo result: $c $b $a;
done
Which of the following are requirements in order to run a shell script like a regular command from anywhere in the filesystem? (Choose THREE correct answers.)
Which of the following SQL queries counts the number of occurrences for each value of the field order_type in the table orders?
Which of the following configuration files should be modified to set default shell variables for all users?
Which of the following is the best way to list all defined shell variables?
What is the difference between the commands test -e path and test -f path?
Which parameter must be passed to ifconfig to activate a previously inactive network interface? (Specify the parameter only without any command, path or additional options)
When the command echo $ outputs 1, which of the following statements is true?
Which of the following details is NOT provided in any output from the netstat utility?
Which of the following tools used for DNS debugging, reports not only the response from the name server but also details about the query?
Given the following routing table:
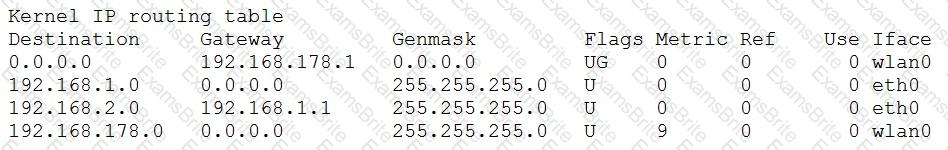
How would an outgoing packet to the destination 192.168.2.150 be handled?
Which of the following commands can be used to display the local routing table? (Choose TWO correct answers.)
Which of the following lines are valid in the file /etc/hosts? (Choose TWO correct answers.)
What of the following can be done by the command ifconfig? (Choose TWO correct answers.)
What is the command to delete the default gateway from the system IP routing table? (Choose TWO correct answers.)
What is the lowest numbered unprivileged TCP port? (Specify the number in digits only.)
Which of the following may occur as a consequence of using the command ifconfig? (Choose THREE correct answers.)
Which of the following keywords can be used in the file /etc/resolv.conf? (Choose TWO correct answers.)
Please specify the top directory containing the configuration files for the CUPS printing system. (Specify the full path to the directory.)
What command should be used to print a listing of email in the system's mail queue?
Which file inside the CUPS configuration directory contains the definition of the printers?
After adding a new email alias to the configuration, which command must be run in order to ensure the MTA knows about it? (Specify the command without any path but including all required parameters.)
Which command is used to sync the hardware clock to the system clock? (Specify ONLY the command without any path or parameters.)
Which option in the /etc/ntp.conf file specifies an external NTP source to be queried for time information? (Specify ONLY the option without any values or parameters.)
On a dual boot system, every time the system is booted back into Linux the time has been set backward by one day. Which of the following commands will correct the problem?
Which of the following are syslog facilities? (Choose TWO correct answers.)
On a system using shadowed passwords, the most correct permissions for /etc/passwd are ___ and the most correct permissions for /etc/shadow are _________.
In case neither cron.allow nor cron.deny exist in /etc/, which of the following is true?
What is true regarding the command userdel --force --remove bob? (Choose TWO correct answers.)
Which of the following commands shows the current color depth of the X Server?
What is the default name of the configuration file for the Xorg X11 server? (Specify the file name only without any path.)
Your senior administrator asked you to change the default background of his machine, which uses XDM. Which file would you edit to achieve this?
What is the name of the simple graphical login manager that comes with a vanilla X11 installation? (Specify ONLY the command without any path or parameters.)
An administrator wants to determine the geometry of a particular window in X, so she issues the __________ -metric command and then clicks on the window.
The X11 configuration file xorg.conf is grouped into sections. How is the content of the section SectionName associated with that section?
Which command can be used to investigate the properties for a particular window in X by clicking that window? (Specify ONLY the command without any path or parameters.)